Season 3 / Episode 29
If movies have taught me anything, it’s that if you want to rob a bank, you dress as the cleaning crew. The people behind the Target hack must have seen one action film too many, because when they decided to hack one of the biggest retailers in the world, they did so via the HVAC maintenance systems.
- Episode 22
- Episode 23
- Episode 24
- Episode 25
- Episode 26
- Episode 27
- Episode 28
- Episode 29
- Episode 30
- Episode 31
- Episode 32
- Episode 33
- Episode 34
- Episode 35
- Episode 36
- Episode 37
- Episode 38
- Episode 40
- Episode 42
- Episode 43
- Episode 44
- Episode 45
- Episode 46
- Episode 47
- Episode 48
- Episode 49
- Episode 50
- Episode 51
- Episode 52
- Episode 53
- Episode 54
- Episode 55
- Episode 56
- Episode 57
- Episode 58
- Episode 59
- Episode 60
- Episode 62
- Episode 63
- Episode 64
- Episode 65
- Episode 66
- Episode 67
- Episode 68
- Episode 70
- Episode 71
- Episode 72
- Episode 73
- Episode 74
- Episode 75
- Episode 77
- Episode 78
- Episode 79
- Episode 80
- Episode 81
- Episode 82
- Episode 83
- Episode 84
- Episode 85
- Episode 86
- Episode 87
- Episode 88
- Episode 89
- Episode 90
- Episode 91
- Episode 92
- Episode 93
- Episode 94
- Episode 95
- Episode 96
- Episode 97
- Episode 98
- Episode 99
- Episode 100
- Episode 101
- Episode 102
- Episode 103
- Episode 104
- Episode 105
- Episode 106
- Episode 107
- Episode 108
- Episode 109
- Episode 110
- Episode 111
- Episode 112
- Episode 113
- Episode 114
- Episode 115
- Episode 116
- Episode 117
- Episode 118
- Episode 119
- Episode 120
- Episode 121
- Episode 122
- Episode 123
- Episode 124
- Episode 125
- Episode 126
- Episode 127
- Episode 128
- Episode 129
- Episode 130
- Episode 131
- Episode 132
- Episode 133
- Episode 134
- Episode 135
- Episode 136
- Episode 137
- Episode 138
- Episode 139
- Episode 140
- Episode 141
- Episode 142
- Episode 143
- Episode 144
- Episode 145
- Episode 146
- Episode 147
- Episode 148
- Episode 149
- Episode 150
- Episode 151
- Episode 152
- Episode 153
- Episode 154
- Episode 155
- Episode 156
- Episode 157
- Episode 158
- Episode 159
- Episode 160
- Episode 161
- Episode 162
- Episode 163
- Episode 164
- Episode 165
- Episode 166
- Episode 167
- Episode 168
- Episode 169
- Episode 170
- Episode 171
- Episode 172
- Episode 173
- Episode 174
- Episode 175
- Episode 176
- Episode 177
- Episode 178
- Episode 179
- Episode 180
- Episode 181
- Episode 182
- Episode 183
- Episode 184
- Episode 185
- Episode 186
- Episode 187
- Episode 188
- Episode 189
- Episode 190
- Episode 191
- Episode 192
- Episode 193
- Episode 194
- Episode 195
- Episode 196
- Episode 197
- Episode 198
- Episode 199
- Episode 200
- Episode 201
- Episode 202
- Episode 203
- Episode 204
- Episode 205
- Episode 206
- Episode 207
- Episode 208
- Episode 209
- Episode 210
- Episode 211
- Episode 212
- Episode 213
- Episode 214
- Episode 215
- Episode 216
- Episode 217
- Episode 218
- Episode 219
- Episode 220
- Episode 221
- Episode 222
- Episode 223
- Episode 224
- Episode 225
- Episode 226
- Episode 227
- Episode 228
- Episode 229
- Episode 230
- Episode 231
- Episode 232
- Episode 233
- Episode 234
- Episode 235
- Episode 236
- Episode 237
- Episode 238
- Episode 239
- Episode 240
- Episode 241
- Episode 242
- Episode 243
- Episode 244
- Episode 245
- Episode 246
- Episode 247
- Episode 248
- Episode 249
- Episode 250
- Episode 251
- Episode 252
- Episode 253
- Episode 254
- Episode 255
- Episode 256
- Episode 257
Hosted By

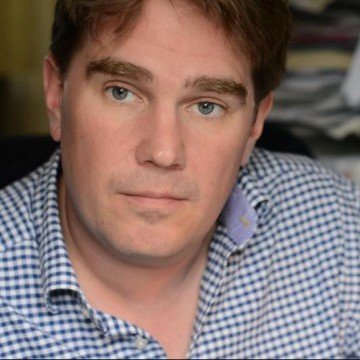
Ran Levi
Born in Israel in 1975, Ran studied Electrical Engineering at the Technion Institute of Technology, and worked as an electronics engineer and programmer for several High Tech companies in Israel.
In 2007, created the popular Israeli podcast, Making History, with over 10 million downloads as of Aug. 2017.
Author of 3 books (all in Hebrew): Perpetuum Mobile: About the history of Perpetual Motion Machines; The Little University of Science: A book about all of Science (well, the important bits, anyway) in bite-sized chunks; Battle of Minds: About the history of computer malware.
Special Guest
Graham Cluley
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s, having been employed by companies such as Sophos, McAfee and Dr Solomon’s. He has given talks about computer security for some of the world’s largest companies, worked with law enforcement agencies on investigations into hacking groups, and regularly appears on TV and radio explaining computer security threats.

Amit Serper
Many of you may have already heard of Amit: he is the researcher who made headlines last June, 2017, when he found a workaround solution that disabled the infamous NotPetya Ransomware. Amit is a long time hacker and spends most of his time reverse engineering malware. Prior to his current position in Cybereason, Amit was a member of an Elite cyber unit in the Israeli government.
Episode transcript:
The Target Hack
Black Friday, 2013.
The biggest shopping day of the calendar year. Americans from all over the country, coming off a recession and finally with some spending money in their pockets, are flocking to retail stores like Target for holiday deals and Christmas shopping. Parents, children, grandparents, teenagers, buying toys, clothes, supplies, electronics, home decor, games. Meanwhile, lurking in the background, a danger that no one could foresee but everyone would soon feel.
At each of Target’s nearly 2,000 store locations, customers push their shopping carts down the store aisles, pick out what they want, then approach a cashier’s desk, swipe their credit cards and head home. Everyone walks out a bit happier than when they’d walked in. What these hundreds of thousands of individuals didn’t know as they drove home from the store that day: they’d just signed away their credit card data to black market criminals.
If movies have taught me anything, it’s that if you want to rob a bank, you dress as the cleaning crew. Okay, movies probably aren’t the best way to learn about crime. Really, if you want to rob a bank in 2018, the best way to do it is, probably, to go in as a hacker. But have you ever seen any of those movies I’m talking about? Usually they’re about small team of quirky, middling criminals trying to pull off “the mother of all heists”. You’ve got a sniper planted on the roof of a building across the street from the bank. The resident hacker sits in a van nearby, relaying information to the team. A couple other guys are armed and ready to blow everything up should the plan go sideways.
And then one guy dresses up as a janitor. Why? Because undercover, he walks right in through the front door. Earlier in the movie they’d probably figured out which cleaning company works in the building, found an employee of that company, and robbed him of his uniform and badge. Now our guy is walking past front-desk security without raising any alarms. Maybe he goes up to the top floor executive’s office, and inserts a malicious USB into the CEO’s computer while they’re in the bathroom. Maybe he’s packed explosives to plant on some big, metal vault door. All the while, any time somebody comes walking in, he has to start sweeping and whistling again. However it goes down, the janitor guy is the most important part of the mission. He’s the one who will give the signal for the plan to commence.
Why am I telling you this? Because when Target was hacked in 2013, it was complicated. It involved a well-crafted, specially-written malware, a small business in Pittsburgh, an unknown backdoor to a large corporate database, a black market financial fraud store and its leader, lawsuits, firings, et cetera. You’ll hear all about that in the coming half hour.
To understand exactly how Target got hacked, though, all you need to do is picture those bank heist movies. The big bank, the cleaning company, the janitor clothes, the plant. And, just like in the movies: it totally worked.
A “Shotgun” Attack
Fazio Mechanical is a Pittsburgh, Pennsylvania-based HVAC company–HVAC as in heating, ventilation and air conditioning. It’s a medium-sized midwestern enterprise, family-run, thirty years old now. Its executives sort of look like Sopranos characters. There’s no obvious reason why Fazio would be in the middle of a major corporate cybersecurity incident, just like you wouldn’t expect your uncle’s garage door company to be at the center of a nationwide news scandal. You could imagine that, of everyone who saw this story unfold and thought to themselves “Fazio who?”, Mr. Fazio himself would’ve been the most surprised of all when the FBI came knocking on his door. “How could refrigeration have anything to do with computer hacking?” he might have said to himself, in his exquisitely-cooled office. Here are today’s interview guests: Graham Cluley, a long time cybersecurity journalist, blogger and podcaster – and Amit Serper, a well known hacker and security research at Cybereason.
“[Graham] So it’s not at all uncommon for a hacker to target a smaller company maybe through a simple phishing attack even and they managed to get a password to log in at that smaller company. They can then maybe access email records and service. They may then be able to steal further passwords. They may be able to plant key loggers, which allow them to then gain access to other systems and they begin to go up the chain.”
“[Amit] Now Fazio Systems had several customers. Target weren’t their only customers. Most of their customers, according to what I saw online, were retail companies. Like Trader Joe’s were there as well and other retailers. Now obviously, they don’t want to travel to their customer site often because their customer sites are all over the US and sometimes they want to connect to their equipment remotely and modify some settings or just monitor it, see how cool or how warm the place is. So they will have access to their equipment, to the HVAC equipment that is connected to Target’s network.
So if you want to attack Target’s network and you as an attacker assume that Target themselves are going to be relatively secure. But you know because you have information about Target using an HVAC provider such as Fazio Systems and you can assume that usually those vendors or those shops basically are not as secure.”
“[Graham]Eventually they found themselves on the Target network and able to access Target’s point-of-sale machines to install their RAM-scraping malware which obviously was capable of stealing credit card information.
So it’s not an unusual type of attack that we see this, this attempt to steal network logging credentials from subcontractors. So my recommendation to companies is you really want to ensure that your suppliers, your subcontractors are taking security as seriously as you are.”
From a hacker’s perspective, using an HVAC contract to breach a major corporation is sort of ingenious. It’s common practice for a large retail company to hire an HVAC contractor to monitor temperatures in their facilities, rather than make that the job of individual workers in every store location. In doing so, of course, the retail company must allow remote access for monitoring temperature, and installing patches and updates to their software.
In this case, our hacker–like just about everyone–had no prior knowledge of the existence of Fazio Mechanical, let alone that they’d be of any significance. Instead, two months before what we know to be “the Target hack” actually occurred, the hacker pulled what’s called a “shotgun” attack, sending out a mass phishing email and, only after receiving data back, deciphering who would make for a good entryway into Target’s systems. The chosen prey, ultimately, was an employee at Fazio Mechanical.
Citadel
The malware sent in an email to this Fazio employee is called “Citadel”–a known variant on the Zeus banking Trojan. The program’s primary function is to steal password information via keystroke logging and form grabbing on Windows OS’s. Zeus had already been well-known to the cybersecurity world, having made trouble for companies as far and wide as Amazon, NASA, and ABC. By 2013, any reputable enterprise cybersecurity software would’ve been able to detect the program as soon as it began to run.
And here is why Fazio was picked on, as opposed to any other Target contractor. Your parents’ laptops have a better cyber defense than the entire Fazio company did. I guess on some level I understand: this was a small business selling refrigerators in Pittsburgh–hardly the sorts of people you’d imagine would be of any interest to hackers. The company’s IT team was made up of zero people (it didn’t exist). The software they used for cyber security: the free version of Malwarebytes Antivirus. To be certain, Malwarebytes is a solid and popular antivirus program for individual computers. The free version, however, provides no real-time scanning function, meaning an intrusion into a system won’t be detected until an administrator runs a test to look. It should also be noted that Malwarebytes’ licensing agreement expressly states it is not made for commercial use.
What this all added up to was the sort of thing you’ve heard many times before on our show. An employee fatefully clicked a phishing link in a malicious email. From there, it was about waiting–waiting, until that employee entered his login credentials for Target’s online work order portal. By logging those keystrokes, the Target hacker gained their janitor’s uniform.
Hacking The Card Readers
Around this point came Target’s first mistake. Let’s say you’re an enterprising hacker, looking to breach a major corporation. What might you have to do? Even if you already have a partnering company’s private credentials, mapping the internal network of a major corporation won’t be easy, and it’ll take a lot of time and resource.
The Target hacker had to do very little of that. Actually, Target did their work for them. A quick Google search in 2013 could’ve revealed Target’s Supplier’s Portal, their Facilities Management and Supplier Downloads page–within which are thorough details about resources available to contracting companies, and how to interact with Target’s systems. In other words: how to look like you’re a real janitor when you walk in the building.
With Fazio Mechanical’s login credentials in hand, the attackers were able to make their entryway into Target’s systems. How, exactly, is to this day not publicly known. Different experts have different views, but the prevailing theory is that the attacker somehow used Target’s “Ariba” portal as their vehicle.
Ariba is the system Target uses to coordinate work orders and payments with contracting companies–perhaps you’re familiar with this kind of thing, if you’ve ever gotten paid online by a company you work for. It’s really boring stuff. However, looked at from a malicious point of view, a portal connecting two computer systems is like a bridge over water. By exploiting Ariba the hacker found their way into Target’s internal file servers. It appears Target’s computer infrastructure failed to isolate its most sensitive assets from the rest of the network, and the attacker was able to move laterally until they reached their jackpot: card readers.
“[Amit] Now the problem was that in IT security, you always want to – when you build your network, when you have a big business, you always want to segment the network in a way that different departments or different pieces of equipment only have access to what they need to have access to.
For example, there is no reason in the world that the HVAC system that was put in Target by a third party vendor/operator, whatever you want to call it, there’s no reason that that equipment should be able to communicate with the payment terminals that are at the cash register area. There is absolutely no reason for that to happen.
Once the attackers had access to the Target network via the stolen credentials from Fazio Systems, they basically had access to the payment devices. They had access to the payment devices because the network wasn’t segmented properly.”
Short of stealing money from a bank vault, hacking a point-of-sale device is one of the most direct ways to steal lots of money, quickly. It’s sort of like hiding in an ATM, and waiting for people to insert their money into your hands.
Security analysts working for Target likely knew of this type of threat, leading at least one to call for a thorough review of the company’s payment terminal protections months before the events of 2013. It’s unclear whether that review occurred or not. Based on the story you’ve been hearing now, I’d bet that person’s warnings went unheeded.
Between November 15th–Thanksgiving–and November 28th–Black Friday–in 2013, the Target hacker successfully uploaded their malware to a small number of point-of-sale devices in Target stores. This, in effect, was a trial run–to see if the malware would work as it was designed to, and to see how system administrators would respond.
Black.POS
First, the malware. Did it work? Yes. Like a charm.
“[Amit] Once they had access to those devices using various methods, they basically created memory dumps of the memory from those paymen t systems and those payment systems, that memory actually holds all of the credit card information, credit card numbers and all of the identifiable information that allows a credit card transaction to go through.
Once the attackers have a code running on those terminals, they can scrape – they can basically scrape the memory from the application that handles the transaction, thus acquiring all the important information that they want to exfiltrate. “
The software used to hack Target was a Target-specific variant of “Black.POS”. Black.POS was relatively new in 2013, but commonly available on cybercrime forums– running at $1,800 a pop for the “budget” version, and $2,300 for the “full” version (“full” in that it allows for criminals to encrypt their stolen data–a real middle-finger to whomever you end up hacking). It’s a program built for point-of-sale machines with card readers, running over Windows operating systems. Most often, vulnerable POS computers are identified for their weak administration credentials or unpatched software. Once uploaded to a POS machine Black.POS works like a charm, reading the information from a credit card strip as quickly as it’s swiped. Criminals are then able to clone credit cards with as much effort as it takes a college freshman to print a fake ID.
That’s exactly what happened at Target stores around America in November, 2013. Once the Target hacker uploaded their malware to every store’s POS readers, he or she became awash in massive amounts of perfectly stolen data from totally unsuspecting civilians. The plan was executed to a tee, and the liquid capital at stake was far more than one person could ever handle themselves.
So who was this Target hacker, who now had 40 million credit cards at their fingertips?
Rescator
December 23rd, 2013. 10:08 AM.
Hi. You better contact me from another jabber that’s not associated with your name, I’ve got an offer for you.
Why from a different jabber?
Because I’ve got an offer for you. So you don’t think I’m trying to play games and fool around with logs after you read my offer.
What kind of offer?
$10.000 not to post your article
Andrey Hodirevski is a handsome, lanky kid with short, brown hair. He lives in Chornomorsk, Ukraine, a port city slightly greyer and more industrial than your average beach town. The kind of place where a kid might get bored and fall into the wrong crowd. On his personal website, Andrey states his life goals: to move to Helsinki, Finland, marry his girlfriend and buy a red, $20,000 Toyota Solara. Also, to achieve world domination. If you were to pass him on the street, Andrey might come across as a college student, maybe an intern at some sort of finance firm. He surely doesn’t look like the leader of an black market cybercrime outlet.
The week after first breaking news of the Target hack, cyber security journalist Brian Krebs took the name of the dark web website where the credit cards were posted–rescator.la–and traced backwards to see what other information might be out there about someone by the name “Rescator”. After some digging, a trail of online criminal activity dating back to 2011 began to take shape, and a historic WHOIS lookup led to Andrey. A social profile of Andrey’s in a Russian gaming forum showed a Skype handle and email address, which eventually led Krebs to earning himself an online chat with the man himself. The person on the other end of the line claimed not to be Andrey, but the $10,000 bribe they offered Krebs to not publish those clues gave pretty good indication that this really was either the target of the Target hack (pun intended), or at least someone very close to it.
Andrey’s claim to fame is as a leader of the Russian-English underground crime ring “Lampeduza”, where he personally operates a series of stolen credit card marketplaces. Among his spoils have been leaked cards from the 2014 hacks of Sally Beauty and Home Depot. Sure enough, shortly after Black Friday in 2013, one of Andrey’s outlets began advertising a new batch of a million cards up for sale.
“[Amit] Carding, which is – what this part of this shady business is called, carding has huge communities both in the clear net and the dark net. There are very large-scale forums where all sorts of shady actors exchange or sell credit card information. We need to understand this data contains names, full credit card numbers. Sometimes it contains physical addresses as well. All sorts of information that makes it easier not only to steal money, but to actually assume someone else’s identity.
Carding networks have all sorts of operations that they run in order to get their information moving from one place to the other, be it – as I said large scale dark web forums or they have like actual money mules that will generate a fake card based on that information that was leaked from such a breach.
They will actually manufacture a card. They will go to an ATM in some country. They will try to empty the account, get as much money as they can, take the cash, go to a Western Union agency and transfer the money to another account. They will do it several times in order to make it harder for the authorities to track the money. These are very large scale operations. These are very – these people are very good at what they do and credit card – stolen credit card data exchanges hands all the time. “
The Target batch was nicknamed “Tortuga”, or “turtle” in Spanish. (Perhaps a dig on Target’s extended failure to respond to their data breach, or just a fun name.) In the month following the Target hack, Tortuga would be updated regularly with millions of new cards.
Andrey really did operate Tortuga like a business–creating a personalized logo for the batch, and advertising a 100% money-back guarantee for any purchases that were found to have been cancelled by the card issuer. The site also featured a versatile search function, where shoppers could filter cards based on the issuing bank, card type, expiration date, even the ZIP code of the Target store location where it was used. It really was like a mini-Amazon.com, except instead of choosing clothes based on your size, here you might choose a stolen card based on the state you live in order to avoid automatic fraud detection from Visa or Mastercard.
On the dark web, Andrey goes by the name “Rescator”. Rescator comes from the name of a character in “Angelique”, a series of French novels. In the series, Rescator is a pirate who commits morally defensible crimes and never reveals their identity. To this day, the exact identity of the Target hacker has not been definitively confirmed.
The Weak Link Is Always The Human
Back to Target. How did they respond to their hack? In short: not well.
The problem was this: we know that the timeline of the attack began on Thanksgiving, and kicked into gear on Black Friday. However, the public didn’t become aware of any of it until December 19th, more than a month after the first system breach. What happened in that month?
In a congressional testimony on February 4th, 2014, Target’s Chief Financial Officer, John Mulligan–Mulligan, like when you screw up real bad in golf–clarified how Target screwed up their cybersecurity. The company didn’t learn that there was anything amiss until December 12th, a whole two weeks after the incident, he claimed, when the U.S. government paid them a visit to give the news.
Perhaps Mulligan was unaware of the real story that would come from Bloomberg Businessweek one month later. It turns out Target had installed FireEye–a business-oriented cybersecurity software–six months prior to November, 2013. As soon as the hacker first uploaded their code to Target’s POS systems on November 15th, FireEye lit up with an unfamiliar detection–named “malware.binary”–and sent automatic notifications to Target’s system administrators. FireEye’s warnings are graded according to the severity of malware detected, and this program was given the highest rating.
“[Graham] Yeah. The weak link is always the human being. The joke is PEBKAC, problem exists between keyboard and chair. It’s the fleshy human always who is the weak link in computer security. Computer security is not a technical problem. The software generally does a pretty good job.”
Target representatives either didn’t see the warning signs, or just didn’t act on them. Postmortem reports speculated the company’s IT department may not have been properly staffed (despite being 300 people deep), or simply may not have fully trusted their new security software. Either way, as FireEye’s notifications kept coming as the attack progressed–this time with the hacker’s server addresses, and escape routes where the stolen data was to be sent–each one, in turn, kept getting ignored.
And if that wasn’t enough: Target had another team located in Bangalore, India whose job it was to monitor their computer systems 24/7. That team notified Target’s Minnesota headquarters on November 30th, that a breach had occurred. It seems no further action was taken.
Symantec–another cybersecurity software installed on Target’s systems–also detected the activity at this same time. Symantec has a built-in feature that deletes malware upon detection. Target had that feature turned off.
This wasn’t just being asleep at the wheel. This was standing in a panic room, alarm bells ringing, red lights flaring, and continuing on with business as usual.
It was December 12th, a full two weeks after Black Friday, when Target was approached by the FBI in regards to a potential hack of their internal data. The following day, executives from the company met with members of the U.S. Department of Justice. The day after that, Target hired a third-party forensics team to investigate. Hiring a team to investigate a hack that revealed itself many times over already was some kind of ironic. It’s sort of like ordering a special third-party investigation into why you touched the stove while it was hot, even after your mom specifically told you not to.
False Information
Target ended up publicly admitting to the breach a week after the FBI visit, and publicly apologized. Before you give them too much credit, it should be noted that Brian Krebs had already broken the story one day before. Target’s executives continued to roll out limited and occasionally false information throughout the aftermath of the story: like, for instance, that credit card PIN numbers weren’t leaked (they were, albeit in encrypted form). The company’s COO, CIO, and President, CEO and Chairman would all resign by Spring of the following year.
“[Graham] At the top level of companies, if they see the CEOs of companies who have been hacked appearing on the TV news trying desperately to apologize or explain what happened and being flustered and all the rest of it, they think, “Crumbs! I don’t want that to be me.”
“[Amit] That’s the point where they really begin to take action and we are now of course beginning to see regulations and legislation where we will have significant finds when customers for instance from Europe are affected by data breaches and there’s a potential to find vast amounts of money. We will have to see if that happens to corporations who have been lax with our data and again, that is something which I think will motivate C-level executives to take security seriously. There really is no excuse anymore. It’s in the headlines. It’s in the newspapers. It’s on the TV news. Every week we are hearing about major high street organizations who are getting hacked. If it hasn’t happened to you already, chances are you will be targeted in the future. So you need to take precautions now to properly defend yourself. Otherwise, you might be that next headline.”
Estimates of the total cost of the breach came in at around 200 million dollars. It’s hard to say how many customers’ credit cards actually ended up being used for financial fraud. Part of the problem was that many of the 40 million customers with compromised card data were also among the 70 million customers whose personal home and phone information was leaked. That meant even if you changed your card’s PIN number, a criminal with your information had just as much authority as you to change it back. Seeing no alternative, some banks such as Citibank began reissuing cards to all clients who could have possibly been affected.
“[Graham] One thing which I think is worth remembering is that when a hacker grabs your details, it doesn’t necessarily mean that they’re going to exploit it in the next three months. It may be – it depends on what data is actually taken. It may be that the data actually has – continues to have a value for six months, a year, three years. So maybe sometime down the road before you actually discover that your details have been compromised or that someone has been phishing you or spamming you or taking out credit in your name and so forth.”
Target itself took a financial hit. In the quarter after news of the breach broke, as retailers around the country saw big numbers in holiday sales, they experienced a nearly four percent drop in income as compared with the same period the year prior.
As part of their recovery effort, Target committed 100 million dollars to upgrade its cyber defenses, including enhanced monitoring and security of internal data, limited vendor access to the company’s own network, and implementation of chip-and-PIN mechanisms for POS devices in all stores. They also laid of 475 workers at their Minneapolis headquarters, and paid $18.5 million in legal damages.
“[Amit] One, this was one of the first big breaches. I think it was Target and then Home Depot and then a few other ones. It raised the awareness of the security of the mag stripe data, of the credit card data. It raised the awareness around properly segmenting your network and securing it and installing more than just a firewall in your network.”
“[Graham] But I think the damage done to Target was quite significant and I think as well it changed people’s view as to what hacks were, the impact it could have. I think many people understood the idea and the concept of you buy something online. You give your credit card details to a company via its website and then they lose that database. People kind of understood that.
With Target, it was something rather different. These were purchases being made in real life at the till, at the checkout. You hand over your credit card or you zip it through the machine. You make your purchase and you’re off. I think many people – rather like with the TJ Maxx hack as well were surprised that actually it could affect you if you’re buying things in real life. The truth was that actually probably had a much more significant impact than any sort of online database breach for online payments being made.”
As concession for the loss of tens of millions of credit cards and personal data files, Target offered customers a one-day deal for 10 percent off on all its store’s products. “Hooray!” said almost no one.
Music & Sound Effects:
https://soundcloud.com/harro94/cash-register
https://soundcloud.com/philip-longman/cash-register
https://www.youtube.com/watch?v=Yj7bVdmcGhg
https://soundcloud.com/cosmiclettuce/dark-tuesday
https://soundcloud.com/jack-winn-2/action-suspense
https://soundcloud.com/edboi19/pirate-tension
Links & Resources
https://people.carleton.edu/~carrolla/story.html
https://mashable.com/2014/03/13/target-hack-ignored/#kn_cNUjexZqy
http://money.cnn.com/2013/12/20/news/companies/target-credit-hack/index.html?iid=EL
https://www.nytimes.com/2014/03/06/business/a-top-target-executive-resigns.html
https://corporate.target.com/article/2014/04/updates-on-target-s-security-and-technology-enhanc
https://web.archive.org/web/20160925225642/http://faziomechanical.com/Target-Breach-Statement.pdf
http://money.cnn.com/2013/12/22/news/companies/target-credit-card-hack/index.html
http://web-privacy.wikia.com/wiki/Target_Data_Breach#cite_note-:0-0
https://krebsonsecurity.com/2013/12/cards-stolen-in-target-breach-flood-underground-markets/
https://en.wikipedia.org/wiki/Rescator
https://krebsonsecurity.com/2013/12/whos-selling-credit-cards-from-target/
https://krebsonsecurity.com/2014/01/a-first-look-at-the-target-intrusion-malware/
https://krebsonsecurity.com/2014/02/email-attack-on-vendor-set-up-breach-at-target/
https://krebsonsecurity.com/2014/02/target-hackers-broke-in-via-hvac-company/
https://www.cyberscoop.com/target-hack-fallout-cybersecurity-rsa-conference/
 Latest episodes
Latest episodes 

 Subscribe
Subscribe 









