Season 3 / Episode 119
For more than a decade, China orchestrated a sophisticated espionage campaign against Nortel Networks, using Huawei, Chinese civilians working in Canada, and even organized crime gangs to steal important technical and operational information. When Nortel finally fell, the Chinese were there to reap the rewards of their death.
- Episode 22
- Episode 23
- Episode 24
- Episode 25
- Episode 26
- Episode 27
- Episode 28
- Episode 29
- Episode 30
- Episode 31
- Episode 32
- Episode 33
- Episode 34
- Episode 35
- Episode 36
- Episode 37
- Episode 38
- Episode 40
- Episode 42
- Episode 43
- Episode 44
- Episode 45
- Episode 46
- Episode 47
- Episode 48
- Episode 49
- Episode 50
- Episode 51
- Episode 52
- Episode 53
- Episode 54
- Episode 55
- Episode 56
- Episode 57
- Episode 58
- Episode 59
- Episode 60
- Episode 62
- Episode 63
- Episode 64
- Episode 65
- Episode 66
- Episode 67
- Episode 68
- Episode 70
- Episode 71
- Episode 72
- Episode 73
- Episode 74
- Episode 75
- Episode 77
- Episode 78
- Episode 79
- Episode 80
- Episode 81
- Episode 82
- Episode 83
- Episode 84
- Episode 85
- Episode 86
- Episode 87
- Episode 88
- Episode 89
- Episode 90
- Episode 91
- Episode 92
- Episode 93
- Episode 94
- Episode 95
- Episode 96
- Episode 97
- Episode 98
- Episode 99
- Episode 100
- Episode 101
- Episode 102
- Episode 103
- Episode 104
- Episode 105
- Episode 106
- Episode 107
- Episode 108
- Episode 109
- Episode 110
- Episode 111
- Episode 112
- Episode 113
- Episode 114
- Episode 115
- Episode 116
- Episode 117
- Episode 118
- Episode 119
- Episode 120
- Episode 121
- Episode 122
- Episode 123
- Episode 124
- Episode 125
- Episode 126
- Episode 127
- Episode 128
- Episode 129
- Episode 130
- Episode 131
- Episode 132
- Episode 133
- Episode 134
- Episode 135
- Episode 136
- Episode 137
- Episode 138
- Episode 139
- Episode 140
- Episode 141
- Episode 142
- Episode 143
- Episode 144
- Episode 145
- Episode 146
- Episode 147
- Episode 148
- Episode 149
- Episode 150
- Episode 151
- Episode 152
- Episode 153
- Episode 154
- Episode 155
- Episode 156
- Episode 157
- Episode 158
- Episode 159
- Episode 160
- Episode 161
- Episode 162
- Episode 163
- Episode 164
- Episode 165
- Episode 166
- Episode 167
- Episode 168
- Episode 169
- Episode 170
- Episode 171
- Episode 172
- Episode 173
- Episode 174
- Episode 175
- Episode 176
- Episode 177
- Episode 178
- Episode 179
- Episode 180
- Episode 181
- Episode 182
- Episode 183
- Episode 184
- Episode 185
- Episode 186
- Episode 187
- Episode 188
- Episode 189
- Episode 190
- Episode 191
- Episode 192
- Episode 193
- Episode 194
- Episode 195
- Episode 196
- Episode 197
- Episode 198
- Episode 199
- Episode 200
- Episode 201
- Episode 202
- Episode 203
- Episode 204
- Episode 205
- Episode 206
- Episode 207
- Episode 208
- Episode 209
- Episode 210
- Episode 211
- Episode 212
- Episode 213
- Episode 214
- Episode 215
- Episode 216
- Episode 217
- Episode 218
- Episode 219
- Episode 220
- Episode 221
- Episode 222
- Episode 223
- Episode 224
- Episode 225
- Episode 226
- Episode 227
- Episode 228
- Episode 229
- Episode 230
- Episode 231
- Episode 232
- Episode 233
- Episode 234
- Episode 235
- Episode 236
- Episode 237
- Episode 238
- Episode 239
- Episode 240
- Episode 241
- Episode 242
- Episode 243
- Episode 244
- Episode 245
- Episode 246
- Episode 247
- Episode 248
- Episode 249
- Episode 250
- Episode 251
- Episode 252
- Episode 253
- Episode 254
- Episode 255
- Episode 256
- Episode 257
Hosted By

Ran Levi
Born in Israel in 1975, Ran studied Electrical Engineering at the Technion Institute of Technology, and worked as an electronics engineer and programmer for several High Tech companies in Israel.
In 2007, created the popular Israeli podcast, Making History, with over 14 million downloads as of Oct. 2019.
Author of 3 books (all in Hebrew): Perpetuum Mobile: About the history of Perpetual Motion Machines; The Little University of Science: A book about all of Science (well, the important bits, anyway) in bite-sized chunks; Battle of Minds: About the history of computer malware.
Special Guest
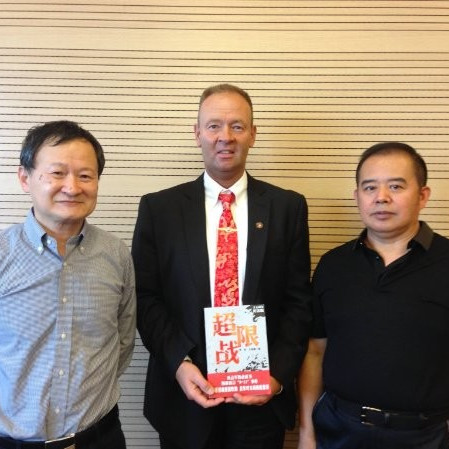
Bill Hagestad
International Cyber Warfare Officer & Independent Security Researcher
Internationally recognized cyber intelligence subject matter expert, providing multi-cultural threat intelligence on global nation state cyber warfare attacks & information warfare initiatives. Clients include global 50 companies across all industries including healthcare, manufacturing, oil & gas, international defense, other governmental agencies (OGA) and cyber threat intelligence.
China's Unrestricted Warfare, Part 3
CHANGE OF CEOS
In 2004, when Brian Shields first notified Nortel Networks’ leadership about a major cyber incident, it’s not that he was outright turned aside. They didn’t laugh him out of the room like cartoon villains. Rather, according to him and others involved, the people in charge just didn’t give it much thought. They were distracted with other matters they believed were more important.
For example, they were right in the middle of firing their CEO, Frank Dunn, for some shady accounting practices. They did so just four days after Brian and his team discovered the breach–so soon that Dunn himself didn’t even hear that he was hacked.
But even those who weren’t fired didn’t hear much about it. Nortel board members later told Bloomberg that they couldn’t recall the news ever having come up in any of their weekly meetings. They were simply too busy with onboarding the new CEO.
The man they brought in was Bill Owens–a decorated former admiral with the U.S. Navy, and former Vice Chairman of the Joint Chiefs of Staff. As CEO he didn’t do anything about the breach, either because he didn’t prioritize it or, if one were to make an educated guess, because nobody around him was talking to him about it. Instead, according to Bloomberg, quote:
“Nortel, a global technological juggernaut, would respond to one of the longest-running Chinese hacks of the decade with a password update and a series of overtures to Huawei.”
Ah, Huawei. You thought we forgot about them.
IP THEFT
As dedicated listeners of this show will know, being anywhere near Huawei–on their radar, to any degree–is a bad idea for Western technology companies. In 2003, a Cisco exec realized Huawei not only copied Cisco’s router technology bit-for-bit, but even plagiarized Cisco’s instructional manuals. The two companies’ documentation contained the same typos. Something similar happened to Nortel.
“[Bill] In one case at least, a piece of network equipment. I believe it was a Wickr was returned to a return maintenance authorization depot or facility in Texas.”
That’s Bill Hagestad: a Retired Lieutenant Colonel of the US Marine Corps, and a frequent visiting scholar to the PLA – China’s People’s Liberation Army. The incident Hagestad is referring to here was verified by a number of Nortel employees, including Shields and a forensic investigator brought in to examine what’d happened.
As the story goes, a Chinese company delivered a unique piece of routing equipment–a fibre card, used in Nortel’s data switches–back to Nortel. They wanted a refund.
“[Bill] The technicians, when they received it, they found that it had been essentially disassembled as if somebody were reverse engineering it. The Chinese didn’t even take the time to put it back together when they returned it and this really kind of tipped the hat that something malicious or malevolent was happening regarding the partnership with China.”
From the National Post, quote:
“Tony Anastasio [assistant to Nortel’s vice president of security] and Brian Shields confirmed the incident, though they say they recall it was a front company that had bought the equipment and passed it on to Huawei. [. . .] Meanwhile, the company started noticing knock-off versions of some of its products in Asian markets, he says. Nortel considered suing, but dropped the matter after the Huawei office across the road in Texas closed down[.]”
Huawei denies ever having stolen Nortel IP. But the allegations against them are numerous. One industry vet told The Globe and Mail that, by 2004, quote: “it was clear to many that Huawei was copying Nortel’s telecom hardware, and even its instruction manuals.” End quote.
Take another example, reported in the Wall Street Journal. Quote:
“On a summer evening in 2004, as the Supercomm tech conference in Chicago wound down, a middle-aged Chinese visitor began wending his way through the nearly abandoned booths, popping open million-dollar networking equipment to photograph the circuit boards inside, according to people who were there.
A security guard stopped him and confiscated memory sticks with the photos, a notebook with diagrams and data belonging to AT&T Corp., and a list of six companies including Fujitsu Network Communications Inc. and Nortel Networks Corp. The man identified himself to conference staff as Zhu Yibin, an engineer. The word on his lanyard read “Weihua”—an accidental scramble, he said, of his employer’s name: Huawei Technologies Co.”
DID HUAWEI HACK NORTEL?
Suffice it to say: if Huawei was behind the Nortel hack from 2000 to 2009, it wouldn’t be surprising, and it wouldn’t be the only way they were spying on Nortel during those very same years.
The circumstantial evidence tying them to the hack can look pretty strong. All you have to do is look at the kinds of information they were targeting. For example, among the information included in those 2004 data transfers to Shanghai Faixan were, quote:
“[S]trategy documents titled “Road-map values and challenges to Nortel,” and “Value Chain Dynamics & Industry Structure.” [. . .] stolen R&D included documents with titles such as “Photonic Crystals and Large Scale Integration” and “Switching and Tuning Highly Integrated Optical Circuits” and “Speed Data Over Universal Mobile Telecommunications Service.”
If a burglar sneaks into your apartment and steals only a certain kind of item–your prized comic book collection, maybe, or your underwear–you can deduce something about who they are. Likewise, none of the information Shanghai Faixan stole would be of much use to anyone other than a fellow telecoms company.
Brian Shields has cited particular files as further evidence. For example, one of the documents from “Live Link” was about, quote, “high speed data over UMTS Quad.” UMTS, basically, is 3G. Four years after the theft, Huawei won its first big North American contract, beating out Nortel in the process. They won on a proposal to install a kind of mobile data network, called UMTS.
HUAWEI’S PLAY
Even though Huawei’s IP theft was an open secret in the telecoms industry, and even though there were signs that they were actively spying on their big brother, Nortel still wanted to play nice. Quote:
“[CEO Bill] Owens met repeatedly with Ren [Zhengfei] about a possible merger. He stepped aside in November 2005 for Mike Zafirovski, who in his previous job as chief operating officer at Motorola Inc. had nearly closed a secret deal to buy Huawei two years earlier. Under Zafirovski, Nortel and Huawei discussed a joint venture in routers and switches, a sale of its Ethernet division, and even a potential rescue during its final weeks.”
Even during these presumably friendly meetings, the Chinese feasted on the gullible Canadians. From Global News, quote:
There were visits by Nortel executives going to China to be wined and dined [. . .] And those executives were told in no uncertain terms by their security, ‘You are being recruited, and they will compromise your computers and cellphones.’
End quote. The Nortel execs didn’t take the warnings seriously and, on some level, can you blame them? This is spy novel stuff. Quote:
“There was detailed actionable intelligence naming people and methods and targets [. . .] “There were people that were caught, and devices found, and backdoors found and traced back to the Chinese. And this was escalated up to Nortel leaders. And they didn’t really want to see it.”
They “didn’t want to see it” because they thought they were doing good business. In reality, the proposed deals Nortel hoped would unite the two companies were, probably, just a front. According to Bloomberg they, quote, “may not have mattered much to the Chinese company, because as Nortel was collapsing, Huawei quietly hired about 20 Nortel scientists who’d been developing the groundwork for 5G wireless technology.”
So, to summarize, while Huawei was feigning business with Nortel on the outside, behind the scenes, they were reportedly bugging Nortel executives, recruiting Nortel employees, stealing Nortel IP, and possibly also hacking them. That last part is still unclear to this day but, frankly, does it even matter at that point?
UW COMBINATION WARFARE
In Unrestricted Warfare, there is a special term for Huawei’s tactics. It’s called “combination warfare”.
According to Qiao Liang and Wang Xiangsui, modern wars can’t be won by a single means. A country with only the strongest army, only the strongest bombs or only the best cyber capabilities will lose to an opponent who can use multiple methods of war in combination–cyber, plus weapons, plus soldiers, plus as many other factors as you can think of. The same can be סsaid, in most cases, of wars throughout history. From “Unrestricted Warfare,” quote:
“King Wu of the Zhou Dynasty three thousand years ago and Alexander the Great over two thousand years ago definitely would not have known what a cocktail was, and yet they were both masters of mixing “cocktails” on the battlefield. This is because, like mixing a cocktail, they were adept at ingeniously combining two or more battlefield factors together, throwing them into battle, and gaining victories. 1+1 is the most elementary and also the most ancient combination method. Long spears and round shields can prepare a soldier for both attack and defense and give a basis for advancing and retreating; two people comprise a unit, wherein “soldiers with long weapons are used for defense and those with short weapons are used for holding positions,” a pair of soldiers coordinate with each other, and then form the smallest tactical unit.”
As much as it refers to spears and shields, combination warfare is also about combining conventional with unrestricted warfare tactics, like economic sanctions, spreading business interests, and using the media to create popular narratives. Like how American government and media worked together during the wars in Iraq, or how Russia uses fake news and cybercriminals to influence international politics in their favor.
Or, in this case, how a company like Huawei might deploy all different kinds of means to gain visibility and a competitive advantage over their larger opponents.
Another entity well-versed in combination warfare is the Chinese Communist Party itself. They’re, arguably, better at it than anyone else. They even have a giant wing of the government dedicated to the task. It’s called the “United Front.”
INTRO TO UNITED FRONT
The United Front is China’s best, sneakiest tool for exerting influence throughout the world. According to a 2018 report from the United States-China Economic and Security Review Commission (or USCESRC for short…kind of), quote:
“United Front work serves to promote Beijing’s preferred global narrative, pressure individuals living in free and open societies to self-censor and avoid discussing issues unfavorable to the CCP, and harass or undermine groups critical of Beijing’s policies.”
There is no exact comparison in the West, but you can think of UF a bit like the CIA, if the CIA employed ordinary American companies and expats to carry out their business. The leaders of the organization are high-ranking CCP politicians, but the real work happens on the ground–in branches located in Chinese communities throughout the world. For instance, in Nortel Networks’ home city of Ottawa, or Montreal, or London, or you name it, there is an arm of the United Front working on what would be best described as influence operations. According to the U.S.-China Commission’s report, quote:
“The CCP’s United Front activities incorporate co-opting elites, information management, persuasion, as well as accessing strategic information and resources. [. . .] It has also frequently been a means of facilitating espionage.”
If this still sounds vague to you, we can clarify by examining a recent example of their work.
UF COVID-19 CASE STUDY
Do you remember, back when COVID first hit, how nobody could get their hands on a facemask? It turns out, you have the United Front to thank for that.
According to the Associated Press, on January 14th or 15th, President Xi Jinpeng distributed a mass notice that Chinese officials begin preparing for a pandemic. Almost immediately, the United Front kicked into gear. From Global News, quote:
“[T]hrough clandestine United Front networks run out of Chinese consulates in cities from Vancouver to Toronto to New York to Melbourne to Tokyo, the Communist Party urged millions of “overseas Chinese” to bulk-buy N95 masks in order to ship “back batches of scarce supplies for the motherland.”
In Ontario, 200 Chinese-Canadians belonging to the Fuqing Chamber of Commerce started driving around to every medical facility they could find, buying up supplies and sending them back to Fujian. Hainan Airlines in Toronto solicited 56 tons of personal protective equipment from foreign government departments, charities, social organizations and Chinese-Canadians. In Montreal, the Chinese Consulate General contacted Canadian government officials, businesses, even student groups to aid in the shopping spree. In Vancouver, a real estate developer started a WeChat group to raise funds and organize mass orders.
As a result of the United Front’s united front, between January 24th and February 29th, 2020, China bought up about 2 billion facemasks. By the time everyone realized what’d happened, it was too late. According to a former Mexican ambassador to Beijing, quote: “In March, the masks sold to China in January and February were being sold back [. . .] at 20 to 30 times the price.”
That, friends, is combination warfare.
Against an apparatus as powerful and well-oiled as the United Front, few individuals, companies or governments could stand a chance. Yet, in the 2000s, that may have been the situation Nortel was in.
UNITED FRONT V. NORTEL
Having studied East Asia for years on behalf of the Canadian Security Intelligence Service, Michel Katsuya had a keen sense of smell for the United Front. He told Canada’s Global News, quote: “I am confident you can see relationships where the United Front Work Department will appear in the Nortel case.” End quote. Another Canadian intelligence expert–kept anonymous for fear of his safety–explained some of the ways China deployed its influence machine in this case. Quote:
“The expert said China’s attack on Nortel had many facets, from systematic hacking and planting of electronic bugs and spies inside Nortel facilities, to usage of Chinese PhD students hired by Nortel to steal research, and attempts to compromise Nortel managers by using spies from the Chinese Communist Party and People’s Liberation Army.”
Indeed, we’re talking about actual spies–Chinese state actors, embedded among Nortel’s ranks, stealing research and committing other manipulative acts. What kinds of manipulative acts, you ask?
Well, consider this: did you find it at all curious that Nortel’s executive management continuously–year after year, without fail–ignored warnings about their breach? That every time Michel Katsuya or Brian Shields brought it up it fizzled out? We assumed that it was just managerial incompetence. But Katsuya himself has a different theory. Quote:
“To this day, I believe there might have been one or more agents of influence controlled by the Chinese in [Nortel] which succeeded in neutralizing our warning.”
In case you didn’t catch it: that was a member of Canada’s premier intelligence service, suggesting that Chinese state spies embedded in the Nortel’s ranks were the reason his and Brian Shields’ pleas about a breach never saw the light of day.
How’s that for unrestricted warfare?
The Nortel story may have involved an email hack, a backdoor, all the stuff you’re used to, but underneath it was far more sophisticated than that. It was United Front statecraft. Combination warfare. Cyber war and espionage and economic manipulation and so on and so on, between the government, at least one corporation, and individuals of all kinds. At one point, quote:
“Canadian intelligence made the stunning discovery that the Chinese Communist Party was using Chinese organized crime gangsters, in attacks on Nortel.”
A lot of groups and individuals with varied interests all got to eat. According to the unnamed expert, quote:
“The best way to describe it is between a nation-state, industry and organized crime, there is cooperation to the point of collaboration and collusion. Spying on Nortel became a requirement that satisfied everyone in that community.”
QIN & ZHAO
China may be the most populous country in the world, but for their entire modern history, they’ve always been behind someone else in line. For a while, it was Japan. More recently, the United States.
Huawei knows that feeling all too well. In its first two decades, the company started by Ren Zhengfei was nothing compared to established, Western megacorporations like Nortel. But Unrestricted Warfare teaches us that little brothers can defeat big brothers, if they just apply a little ingenuity.
AUTOPSY
China never had the resources or the talent to compete with the West in technological supremacy. Huawei didn’t have nearly enough to compete with Nortel. But they effectively took advantage when North America’s foremost provider of internet wires was busy with executive infighting, bad accounting, stock losses, and all the other issues that crop up when a company gets too big for its own good.
“[Bill] So this was really the undermining of Nortel before the Chinese came on the scene.”
Bill Hagestad again.
“[Bill] The Chinese simply took advantage of a market evaporation that Nortel’s executives essentially created for themselves focusing more on the quarter by quarter results whereas the Chinese look at in a very long range plan.”
Nortel was going to fail whether or not the Chinese had a role. The company was beset by failures in management and finances ever since the Dot Com bubble. But, like hyenas encircling the injured gazelle, the Chinese ensured their fate, and reaped the rewards of their death.
“[Bill] the tale of Nortel and Huawei is really a duality in the failure of corporate leadership within a Canadian enterprise and the Chinese actually taking advantage of that weakness. You can imagine that they read Sun Tsu probably and study it more than we in the west do. [. . .]
I won’t say that I – my hat – I tip my hat off to Huawei doing this because I give them the quarter on social media and they know that and they don’t like me. The fact is that they were successful in infiltrating and perhaps accelerating the demise of Nortel through this three-prong strategy that they took advantage of successfully.”
MADE THEIR BED…
admittedly, when I hear the story about Nortel helping build to censor the internet and then getting hacked by a company that was largely boosted by this whole effort. It gives me a little bit of schadenfreude and at least in the way that I framed this story in my head. It’s sort of Nortel makes their bed and the lays in it. Am I justified to feel this way or is there something I’m getting wrong here?
“[Bill] No. You’re actually reading it 5 x 5 as we say in the military communications world. You’re reading that accurately. Certainly, there are the nationalists in us and perhaps those that are taken offense to that, but indeed it is correct. Nortel became its own worst enemy through corporate infighting and then allowing essentially the Chinese to take advantage of perhaps bordering on illegal activity although it’s never necessarily been proven through hacking, through intellectual property theft, through the compromise of credentials of executives who had the wherewithal and the nuances of Nortel strategy. They took advantage of it.
So really, they – if there’s egg to be flown or worn by anyone, it is really those executives from Nortel and certainly the over-aggressive initiatives of the Chinese government vis-a-vis their hacking cadre to take advantage of that.”
HUAWEI OTTAWA
These days, the biggest telecom company operating in Ottawa has their research lab just a ten minute’s drive from Carling Campus. All you’ve got to do, coming from Carling, is take a left, another left, a right, and you’re there. 303 Terry Fox Drive, Huawei Ottawa Research & Development Centre.
Huawei Ottawa has been home to truly cutting-edge wireless telecommunications research, not least because they have some very talented people working there. Some of those people arrived at 303 Terry Fox after years working just down the road.
“[Bill] during the demise of Nortel, many of the very credentialed experienced scientists, engineers of Nortel were hired away by Huawei to work on what they ultimately have ruled out as the precursor to 5G.”
At Huawei’s HQ in Shenzhen, a “wall of fame” for the company’s brightest stars includes quite a few Canadians. One former Nortel employee who visited the site told the National Post, quote:
“These are (now) Huawei employees associated with great technological accomplishments … and I recognized so many of them. [. . .] At one level you’re proud to be a Canadian, at the same time you’re upset to be a Canadian.”
“[Bill] So one could say that from the ashes of a Canadian company came the bird of prey of China’s Huawei.”
Huawei is now the biggest telecom in the world. The Nortel Networks of our day, you might say.
CARLING TODAY
Nortel itself is long gone. If you drive into Carling Campus today, you’ll be stopped early–even before you can go inside–by a checkpoint guarded by armed military.
Back in 2010, to wind down their bankruptcy yard sale, Nortel auctioned off their giant Ottawa headquarters. The deal went to Canada’s Department of National Defense–their equivalent of the Pentagon–for 208 million dollars.
Soon, they began revamping the beautiful but, frankly, declining infrastructure. From the Ottawa Citizen, quote:
“For instance, the project has had to shell out $7.5 million more than expected to bring the Phase 1 buildings up to code to withstand seismic activity. It has also budgeted an extra $31 million to replace defective windows.”
Must’ve been a lot of crappy windows.
The entire renovation effort cost the DND around $700 million dollars–everything necessary to get the facility to military standards. And it included a full sweep, to make sure Nortel didn’t leave anything behind. That sweep ended up yielding some interesting findings. In an interview with the Citizen, a Vice Admiral from DND in vague terms, quote: “legacy bits and pieces, whether they were intended to be there or not.” End quote. He was referring to something they found in the buildings. He went on to say, quote:
“The whole facility was swept when we went through in preparation for our moving in. Anything that was there was legacy to what I would characterize as industrial activity and we are completely satisfied now that this is a site we are able to move into and it meets all of our security requirements. I am assured anything that was there is no longer there. … It was all legacy, old-school stuff associated with the previous occupant.”
End quote. Did you notice anything weird in that statement? The admiral references something which sounds kind of…bad.
Other DND personnel later clarified what the statements were in reference to. In their sweep, they’d found multiple listening devices–hidden microphones that were no longer active, because the previous tenants had moved out.
It’s funny, in a way. The espionage campaign that went on for a whole decade lasted even longer than Nortel itself.
 Latest episodes
Latest episodes 

 Subscribe
Subscribe 









