Specials & Interviews / Interview Special – Graham Cluley
As we prepare to release an awesome 2-part story in two weeks, we decided to give you a chance to go back to some old favorites and check out some of the behind-the-scenes interviews of Malicious Life.
Graham Cluley tells about his entry into the world of security. There are stories aplenty in this interview- Graham tells of how he turned from a young student writing video games for donations, to a programmer for one of Europe's leading anti-virus solutions in the early 90's, and sheds a ton of light on the malware industry in some of its earliest days.
Pair this interview with Episode 2- The Dark Avenger, for a comprehensive view of the virus (and anti-virus) writing scene of the early 90's.
- Amit Serper Interview – Holiday Special Episode
- Interview Special – Graham Cluley
Hosted By

Ran Levi
Born in Israel in 1975, Ran studied Electrical Engineering at the Technion Institute of Technology, and worked as an electronics engineer and programmer for several High Tech companies in Israel.
In 2007, created the popular Israeli podcast, Making History, with over 10 million downloads as of Aug. 2017.
Author of 3 books (all in Hebrew): Perpetuum Mobile: About the history of Perpetual Motion Machines; The Little University of Science: A book about all of Science (well, the important bits, anyway) in bite-sized chunks; Battle of Minds: About the history of computer malware.
Special Guest
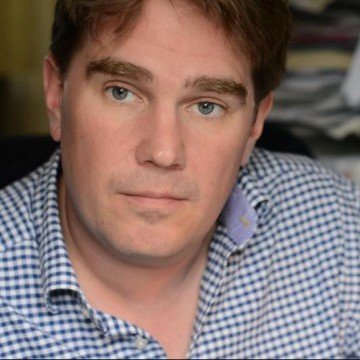
Graham Cluley
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s, having been employed by companies such as Sophos, McAfee and Dr Solomon’s. He has given talks about computer security for some of the world’s largest companies, worked with law enforcement agencies on investigations into hacking groups, and regularly appears on TV and radio explaining computer security threats.
Episode transcript:
Ran: OK. So let’s start with you introducing yourself and tell me how you started in information security.
Graham: Ha! Well—yeah. So my name is Graham Cluley and I’ve been working in the field of computer security since round about 1991, I think, or 1992 when I began my life as a programmer at a company called S&S International who produced pieces of Dr. Solomon’s antivirus toolkit which was one of Europe’s leading antivirus products at the time, and Alan Solomon was a real guy and he needed a Windows programmer. And I came into the industry by a rather strange route which is that when I was at college, I had been writing computer games and at the end of my computer games, it would put up a very sad message about how I was a poor, impoverished computer programmer. And if only people would send me a check for 5 or 10 pounds, I would be able to fulfill my dream of visiting my girlfriend who is studying in Paris and go down to the supermarket and buy her a trolley-load of cheesy biscuits. And people liked my games, and they did that, some sent me some money which was fantastic at the time, you know, I was just a young student.
And one day, I got back home and there was a big box on my desk—oh, sorry, box on the front door and I opened it up and inside was a copy of Dr. Solomon’s antivirus toolkit, which is very nice. I checked for 20 pounds, much more than I’d asked for and most importantly a packet of cheesy biscuits. So I hadn’t had to go down the supermarket. And there was a letter from Alan Solomon saying, “My kids love your games. If you want a job, get in touch.” And I was desperate for a programming job at the time, and so I thought, “OK, I’ll do that” and it turned out I was one of the very first programmers at his company and I wrote the Windows version of his antivirus software, but—
So, all happened by accident. I did have an interest in computer viruses before then like many people. It was the early days of the internet at our college and we didn’t have the web. The web didn’t really exist back then. But we had used net and we had mailing lists, and one of the many mailing lists I was on was Virus-L which was the digest of the comped up virus mailing list. And so, I was interested in reading about malware or as we then called—it was mostly viruses and Trojans back then. We didn’t really—
Ran: Yeah. Why did you—why were you so interested in viruses?
Graham: To be honest, I was doing a computer studies course and it wasn’t something which particularly fascinated me, computer viruses back then. But there wasn’t very much on the internet to do and so I joined all kinds of mailing lists. So I was on a mailing list, for instance, about cryogenic suspension. There was a guy who said, “Look, if any of you are about to die, send a message to the mailing list. I’ll come around with my fridge freezer and freeze your bodies.” So I was on that mailing list and I was on mailing list for all kinds of things and one of them was this virus thing and I thought, “Well, I’m into computers. I might as well read about this on what’s going on,” you know. We didn’t have the web, you know. We didn’t have smartphones. What could we do to entertain ourselves during lectures other than read about cryogenic suspension or these mysterious things called viruses? So that’s what I was doing.
Ran: So I guess we should be grateful that the cryogenic industry has not evolved as well as information security.
Graham: Yes. I think it’s a—yes. Their loss is hopefully information security’s gain, but there won’t be out there to disagree with that.
Ran: So talking about mysterious viruses, what did you know about viruses back then? What did you think about them?
Graham: I think I believed that they existed and I know that seems a crazy thing to say. But at the time, there was a lot of myth about computer viruses. Some people I think actually was—you know, way back then, in the late ‘80s and early ‘90s, I think it was Peter Norton himself who said that viruses were an urban myth like the alligators in the New York sewers, and about 18 months later, Symantec released the first version of Norton antivirus.
So there were a lot of people who simply didn’t believe they exist. They thought this is all just hype. People are just buying snake oil to protect themselves against something which people— You have to remember most computers at the time weren’t even networked, let alone on the internet. And so the only way you could catch a virus was from someone handing you a floppy disk and you’re putting the floppy disk into your computer and maybe you’re booting off that floppy disk. You see that non-system disk carry a message and the virus jumps onto your hard drive. That was the way in which viruses spread at the time. So, it would take months and months if at all for a virus to spread around the world by basically sneaking it.
So, malware was much less commonly encountered and yet you kept on hearing stories about people who supposedly had had something bad happened on their computer. Some people didn’t believe it. I did believe it existed. I mean I think the mailing list I was on helped convince me that these were genuine problems albeit nothing like the scale which we’re on now.
Ran: When was the first time you actually encountered a virus in real life or then infected by a virus?
Graham: Well, I’ve been remarkably lucky in my own life. The only times in which I’ve actually come across actual virus-infected computers has been on other people’s computers. My own computer unless I’ve deliberately infected it, I’ve never had an infection. I have had situations where—I remember once we were having a conference and our company was organizing it and there were virus experts from all around the world and we’d say, “Oh, can you give us your slides?” and things like this and they’d give us a USB stick or a floppy disk, and we’d put it into our computers and the antivirus goes “Zoop! Zoop! Zoop!” which say, “Excuse me, Mr. World Famous Virus Expert,” I’m not going to name any names here, “You appear to have given me a virus to—” Back in those days, people were a lot less careful in some cases. So I’ve not had that happen myself.
But even way back then in those early days, I realized the importance of computer security. One of the things—as I said, I was writing computer games. One of the things my computer games would do would be an integrity check on themselves. They would do a check on themselves to see if they had been altered and refused to run because I just thought, “Well, that’s a sensible thing to do because you don’t want someone meddling with your files.” Now, that might—that probably wouldn’t have successfully prevented the infection from what we call a stealth virus. But for many common viruses, that would have been enough to identify that something fishy was going on and prevent it from happening. So—Yeah. So, I’ve never really got infected myself unless I’ve wanted to. But, of course, like everyone who works in this field, we have friends and family and colleagues and relatives who—
Ran: And you become the tech guy for the family.
Graham: Yeah. Yeah, you do, don’t you? And, you know, I think that’s the price we have to pay for being in this industry is we can share some of our knowledge with others and—I think it’s an awful shame when computer—I mean computer crime in all its forms, and way back then, it was just purely graffiti really. It’s such a shame when that puts people off using computers because computers are incredibly enabling devices which help people keep in contact with each other. And I’ve always thought it’s just such a scoundrel thing to do to write computer malware. I’ve never been tempted to write a virus or anything like that. That’s the other conspiracy you have not only in the early days, you know, “Do viruses exist?” But then they go, “Oh, but I bet you write them, don’t you?” I say, “No, we don’t,” you know. We wouldn’t do that. We’re the nice guys.
Ran: Has anyone ever accused you really of creating viruses and then fixing the problem?
Graham: Oh, yeah. I mean that—you just hear that all the time. And—you know, you come up with all kinds of funny answers to that thing because that’s the thing you used to hear the most often. And so you say things like, “”Yes, yes, of course, I write the viruses and I was on the grassy knoll that faithful day in November 1963 when President Kennedy went past,” you know, it’s—let’s get all the conspiracy theories out. You say, “Oh, yeah. Why would we write viruses when there are plenty of kids writing them for us for free?” You know, why would I get paid by my company to write malware when there are—you know.
It’s interesting. The situation has evolved so much. Way back when I started in the computer security industry, there were round about 200 new computer viruses every month. And most of our customers would receive their security updates or antivirus updates on a floppy disk sent to them through the post. It’s crazy, isn’t it? And the most frequent that you could get those updates was monthly. Most of our customers got them every 3 months and that was good enough.
And over time, we began to offer them on bulletin boards for people to download and things like that, but we even had a system where if there was a big outbreak, you could read out the antivirus definition because it was just in hexadecimal. You could read it out down the phone or fax it to someone and get them to type it in. But those days are gone, of course. It’s no longer 200 viruses a month. Now there’s, what, 300,000? 400,000 a day? You know, it’s—
Ran: Maybe even an hour.
Graham: Yeah. It’s—
Ran: Probably.
Graham: The numbers are completely huge.
Ran: It should be remembered that many of the magazines back then—I was—these early days, I was a Spectrum guy—
Graham: Oh, yeah.
Ran: The Spectrum machine?
Graham: Yeah.
Ran: And we used to get floppy disks and later CDs via magazines. They had CDs attached, so—
Graham: Yes.
Ran: Floppy disks attached, and sometimes they would carry viruses as well.
Graham: Absolutely. That was an incredible—that happened all too often, was that these magazine cover disks would contain a virus and, of course, that would be an incredible way to kickstart a brand-new infection and spread it around. And there were major viruses which was spread that way. I remember, for instance, the Chernobyl virus, also known as CIH, that was spread on a floppy disk. The Marburg virus, one of the very first Windows 95 viruses, was spread on a floppy disk attached, you know, Sellotaped or CD-ROM attached to the front of a magazine.
And way back in the early 1990s, the antivirus company I worked for, one of the services we gave magazines was we will scan your floppy disk before you put it on the cover of your magazine to make sure that it’s squeaky clean. And eventually, we got out of that business because we just thought, “You know what, this is too risky. There’s so many programs and they’re crammed in there and they’re compressed in multiple ways and so many accidents can happen along the way that maybe we don’t want to be the company which—”
Ran: Responsible.
Graham: Yeah, because we would get the blame. It’s like, “You know what, this—you’re getting all this software from unknown sources and even if we can detect known malware on it, there’s also the potential someone could have embedded some sort of Trojan horse deep in the code, which we simply wouldn’t pick up.”
Ran: Yeah. And you said that these early viruses were kind of like graffiti. In what sense?
Graham: Well, in the early days, there wasn’t much point to writing a virus. Usually, they were being written to show off to their friends, to their peer group. And so—in fact, I miss those days because the viruses back then was so much more visual and graphical, and so they would put funny messages up on the screen or that have some ASCII art or letters would drop down the screen or you’d have a green caterpillar crawling across the screen eating up your letters and pooing them out the other end brown. You know, you knew when you had a virus.
Ran: That one I’ve never heard about.
Graham: You never heard of green caterpillar? Oh, add 1575 bytes to the end of your executive file. That’s the kind of—useless, useless trivia which you learned as a computer security expert about the early virus. You can ask me about modern viruses. I won’t remember anything about them. But the ones from way back then, you remember even how many bytes long they were because it was just—you know, that’s what you had.
But, yeah, so viruses way back then would do something visual because they needed to announce their presence or they’d play a tune through your speaker and, you know, even the typical guy in the accounts department would know that something bad had happened. And the reason why they were comfortable telling people that they existed was because they weren’t stealing money. They were just purely graffiti. They just wanted to make the headlines, some 15-year-old boy, and it was typically men who were writing these things at the time. They didn’t have enough vitamin D and maybe they don’t have a girlfriend and, you know—they were just too obsessed with computers and writing these things in the underground community. But they weren’t doing it for money, and that was one of the big changes which happened, of course, was because when they started being financially-motivated, you didn’t want to announce your presence. You didn’t want to tell people that you’d compromised their computer and maybe was stealing information from you.
Ran: When did you realize that the landscape of information security is changing towards the more sinister economical-motivated malware?
Graham: I think it really began in the late 1990s when—although there was still a lot of juvenile activity when it came to malware. Those were still things you didn’t want, right? You didn’t want to pass them on to your customers. They were still a serious problem and you wanted to stop that stuff, but it became oh so much more serious when the password steal has begun to arrive, and the password steal as I would argue first really began to see a big movement of them towards the end of the 1990s particularly with AOL password stealer, software specifically written to grab the passwords of AOL users because everyone wanted cheaper internet. And so, you would grab the details of people that way. And that began to evolve over time into more general password stealing, so it might be your internet dial-up passwords but, of course, it may also be the passwords you are using to log in to websites, to log in to your online bank and those attacks over time became more and more stealthy, so they wouldn’t announce their presence. There would be no benefit to them going, “Yohoo! I’ve infected you.” There was no point to that.
Ran: And by the way, it’s interesting to note that today’s ransomware has kind of reversed that—
Graham: It has.
Ran: Because now you have to notify the user that you exist and you want money.
Graham: Yeah, and we’ve seen some creativity and some artistry now in ransomware, you know. If you’re writing a piece of ransomware, one of your questions must be, you know, “How are we going to depict a great big skull dripping in gore and blood on the screen? How are we going to grab people’s attention here?” So, I think you’re right. It is a kind of reversal because they have to tell people, “Hey, you are infected. You are going to have to pay us money to get your data back,” and obviously, ransomware is one of the most pernicious things.
The other area where we saw that kind of return to creativity is through website defacement, of course, and some hacktivist activity where the hacktivists not necessarily doing it for money but they want to embarrass a company or they want to expose poor security or they want to reveal the secrets of a company, or maybe they’ve just got revenge in mind against the big corporation. I mean we saw the Sony hack, for instance. Many people said it was North Korea who were behind the Sony pictures hack. I don’t know necessarily that that was true or not. I suspect it may not have been true. But one thing it did was it displayed very graphical images on the screens of Sony computers and, you know, it was designed to get attention and by word it did.
Ran: And speaking of hacktivism, I mean the mainstream media tends to see groups such as Anonymous as a kind of representative of computer hackers in a stereotypical way I guess.
Graham: Yeah.
Ran: The people who used to write malware in the early days where they like Anonymous in the sense that they were anarchists just having fun or was there any other behind them?
Graham: I think many of them in the early days were really doing it for fun because they were into computers and they wanted to hang out at least electronically with other guys who shared the same interest. And they would create alter-egos for themselves so they would have these fanciful names like Nowhere Man and Patchy Warrior, Ice-9, Colostomy Bag Boy, you know. They would have these—and it was a bit like, you know, thinking of members of the World Wrestling Federation, you know. They have all this bravado and they have this great big name but, you know, in reality, that wasn’t what they were at all. But they had this alter-ego online where they would, you know, describe themselves as dark, phantom or something like that and it’s like, “Come on.”
Ran: There was the Dark Avenger, if you remember.
Graham: Dark Avenger, yes. Dark Avenger from Sophia in Bulgaria who was—he was a virus writer who got an awful lot of attention through his malware which he has written, which was quite a sophisticated malware. He also wrote this thing called The Dark Avenger Mutation Engine which you could plug into your own piece of malware in order to make it polymorphic to try and avoid detection by antivirus software.
And a lot of the media then began to think, “Will all virus writers come from Bulgaria?” You know, that’s the center, but it’s like, “No, not really. You know, these viruses are being written all over the world. You don’t have to be in Bulgaria to do this.” And, of course, that continues to this day. There are malware authors and hackers probably in every country.
Ran: Did you have any personal encounters with virus authors in your line of work?
Graham: I’d sometimes met them at computer shows, so you’ll be, you know, manning the booth at some ghastly computer show and members of the public come up to you and ask you questions and occasionally someone would come up and say, “Hi, I’m Garbage Heap.” It’s like, “Oh, really? Do I call you Garbage or Mr. Heap?” you know, and he might talk about whatever you said about his virus and you tell him something about his virus and you have that—those kind of conversations. It doesn’t tend to happen as much these days obviously because I think the typical malware author realizes just how much serious trouble they can get into.
But back then, certainly it did happen. Normally though—I mean you wouldn’t meet these guys in person. There was one female virus writer called Gigabyte. She was a Belgian virus writer and she took particular offense to me. It was all a misunderstanding. She—but it played out in the media. I think the media liked that she was taking pops of me and I was sort of taking pops back. And so occasionally she would mention me and her viruses and the reason why she mentioned me was she thought I’d said that girls weren’t clever enough to write viruses, and that is not true. I’ve never believed girls aren’t clever enough to do anything. In my experience, they do just about everything better than us dumb men.
But what I was saying was that girls are too smart to write viruses. They’ve got better things to do at that time. Remember, these are the days before you made money out of malware. And so, my whole point was women have got better things to do at that time than this childish pointless activity which men do which is writing viruses. And I mean she got upset and she wrote some viruses which mentioned me by name and the most notorious one is one called Coconut. It’s displayed a picture of my head on the screen and you had to throw coconut at my face. And I think the more times you hit my face with a coconut, the less files she would infect from your computer, so there was a real incentive to hit me in the face with a coconut. You know, that’s quite witty because—
Ran: Were you flattered?
Graham: Well, you know, it’s—you know, I’d rather she hadn’t written a virus at all, but then if you’ve got the choice of using my face you know, I think, “OK, that’s nice of her.” But because I’m a little bit childish and silly, when the media rang me up about this and said, “Why do you think she’s doing this?” I couldn’t resist saying, “I think she’s probably got a little bit of a crush on me.” And so—and, of course, that just wounded—it just wound her up even more. She was eventually identified and the police had to work with her. And now she works, I believe, as an IT technician. You can find her on Twitter. She was never imprisoned or anything like that for her viruses and she seems to have gone to the good side. I think actually I might follow her on Twitter. I’m not sure.
But, yeah, she is out there. I’m afraid romance never blossomed, but the media loved it because she was a very—I mean she was at that time a very rare example of a young woman, blond with a ponytail who wrote viruses and so the media loved it because they kind of pictured her as a Lara Croft kind of figure and sometimes she did appear on TV and things.
Ran: Yes. I remember she used to practice kickboxing I think.
Graham: Yes, that’s right. Yes. Yes, that’s right. I was once asked by a security company could I go and give a talk at their conference and I said, “Yeah, sure.” And they said, “Oh, we’re trying to get Gigabyte along as well.” And they said, “If we managed to get her to come along, would you mind doing karaoke with her on stage?” which is one of the most bizarre—
Ran: Why karaoke?
Graham: –most bizarre—oh, and I love karaoke. But one of the most bizarre requests I’ve ever received. Anyway, it didn’t happen I’m afraid so there’s no secret album out there which people can purchase of me and Gigabyte.
Ran: And you didn’t contact her or make any communications later on I guess?
Graham: We’ve chatted via Twitter occasionally in recent years but, you know, very sort of briefly but that’s been it. So I’m afraid romance hasn’t blossomed.
Ran: She what—she apologized I guess or whatever? Or not so?
Graham: Not that I remember, but then she probably feels like many virus writers from that time do. She probably feels, you know, what she did was quite unimportant. And certainly in the context of today’s malware, it was kind of trivial. You certainly didn’t want to on your network and it could disrupt your company’s business and, you know—no malware is good in my view. You know, the clue is in the name, right? It’s malware. But, there are different shades of evilness and probably her malware was a lot less evil than certainly some of the stuff we see these days, which is completely, you know, abhorrent.
Ran: What is, let’s say, your personal interest in the area of information security? What of the various threats and fields is the most—you find most interesting?
Graham: I guess I find interesting how serious things have become and the growth of state-sponsored malware. We never imagined—you know, the antivirus industry has been going round about 30 years and we never ever imagined that governments would be writing this kind of stuff, not just occasionally. They’re writing it all the time, the amount of spying which has gone on over the internet and it kind of makes sense if you think about it. It’s so much easier to spy on someone via a computer where they have a webcam in front of them, where they have a microphone turned on permanently, where they have all of their files on that device that you want to steal. So much easier to grab those control of those devices than is to parachute James Bond in Behind Enemy Lines and tell him to steal some microfilm. And you have this wonderful benefit of deniability as well because it’s so hard to attribute an attack to a particular country and say with complete confidence it was the Russians, it was the Chinese, it was the British, it was the French. It was the Israelis who did this. It’s so hard to prove that that it makes it fantastic for surveillance and espionage. And—so that’s very interesting to me.
The other sort of oncoming storm, if you want to call it that, sort of thing which is rapidly approaching us and which I think is a nightmare is the Internet of Things where every device now is getting a computer chucked in it with very little thought as to security and default passwords and they’re made on the cheap and there’s no updating infrastructure. And these devices as we know from recent events are already being compromised and hijacked and used for denial-of-service attacks and all manner of other attacks as well. So, that’s kind of scary that we’re making big mistakes.
I think the computer industry has largely learned—has learned a lot of lessons from fighting this war for the last 25-30 years. And so operating systems are being hardened and, you know, we all recognize what needs to be done I think to protect—we don’t know how to do it perfectly but, you know, protecting systems and services are understood. But these new devices have come along from many factories who have no history and no past knowledge of how to do this properly and, you know, it’s going to be a big fight.
Ran: Those recent attacks that you mentioned in—talking about IoT are, of course, DDoS attacks. When did the DDoS attacks begin—let’s say, when did DDoS attacks start to become a real nuisance in the internet?
Graham: Well, I think if I recall correctly, the DDoS attacks really began to become influential round about the time of the rise of the botnet. So, when the hackers realized that they shouldn’t just compromise computers to steal passwords, but they could actually compromise them to hijack resources, to send spam and to have all of those controlled at once. And then you think, “Well, we don’t just have to send spam from these computers,” which is one way of monetizing them. “We can also extort money by launching DDoS attacks as well.”
So the botnet—the rise of the botnet, the idea of so—and I think that this was really, if I recall correctly, the early 2000s when this really began to become a problem—new bot software coming out compromising computers, being under the control of one bot master. And, you know, there is so much being done and so many attacks which are constantly happening against websites now. There’s a thriving industry of companies who are trying to mitigate DDoS attacks as well. And there are companies who are prepared to pay a large amount of money to stop a DDoS attack, I’m afraid.
So—I can kind of understand that in a way because they want to do business. If a gambling site is targeted with a DDoS attack just before a big sporting event, and they think, “If we aren’t running on this particular day, we are going to make—we’re going to lose a lot of money.” They’re making a pragmatic business decision to pay the extortionists. I don’t like it, but I can kind of understand it. Similarly, I don’t like it when people pay ransomware demands, but I can understand if you’re a business and you’re going to go out of business if you don’t pay that $5000 or whatever it is that you’re going to pay. And that, of course, is what’s causing so many more attacks to happen all the time.
Ran: The latest DDoS attacks were huge in terms of bandwidth. Do you think that DDoS attacks can become a major threat that really disrupts the activity of, let’s say, large organizations? I’m talking about Amazon, Google-sized organizations. Or, will the industry know how to deal with these growing and growing attacks?
Graham: It’s always difficult to make predictions as to what’s going to happen, but I also think that we shouldn’t be complacent and think, “Oh, that could never happen.” I think the history of computer security has shown us that there have been many occasions when we’ve been surprised as to what’s being possible and what’s being achieved. And the recent DDoS attacks, they didn’t bring down a site as big as Google but they did, of course, disrupt large parts of internet infrastructure, many major sites. So, if you attack companies like that, if you manage to bring down companies like that, that has a knock-on effect on so many other services as well. So, I don’t think we should be complacent about this and that really sort of leads again back into my fear about the Internet of Things. So many more devices plugging into the internet which are poorly secured. We are only just beginning to get to grips with computers connected to the internet. We’re only just beginning to get rid of all those Windows XP computers, which are poorly patched and, you know, there’s still some really old pieces of malware doing the rounds, which we first saw years ago. But they’re still spreading because there are still devices out there which aren’t properly patched to prevent them from spreading. So, it’s a worry.
Ran: That’s an interesting notion that today’s cyber’s fear is still full of old malware making the rounds.
Graham: Yeah. And, and—
Ran: Is that true?
Graham: And there are servers which will probably never be patched. There’s pieces of malware which will never completely die and which would just carry on just pinging around a little bit, you know, between some computers which people have forgotten about, but in their cupboard, they got plugged in under the desk, never gets patched and it’s infected and it’s looking for other devices to infect constantly. So, yeah, there is old malware which continues to cause, you know, not headline-making problems but it’s still out there like a background radiation.
Ran: That’s an interesting comparison to background radiation. I love that. And still on the subject of DDoS attacks, were your site or blog or your company’s site ever attacked in that way?
Graham: Oh, yeah. Yeah. My site has been attacked a number of times with DDoS attacks. I don’t quite know why. Well, I got a feeling as to I know why. There was a series of attacks which were happening last year against some of the anonymous email companies, companies like ProtonMail and others. I think ProtonMail ended up paying a ransom demand if I recall correctly after they were hit by a DDoS attack. And I wrote something saying they shouldn’t have paid and, you know, they’ve just encouraged it and the attackers are going to attack more and more, and indeed they did attack ProtonMail again.
And, I suspect that upset a particular group who were launching the DDoS attacks that I was saying “Don’t pay. Ignore—you know, put your defenses in place. That has to be a better answer.” And sure enough, my site has been attacked as a result. I now—I’m fortunate enough. My site is protected by a DDoS mitigation service. I wouldn’t be able to afford it myself because I’m just a one man, you know, one man and his dog in his back bedroom blogging. They were kind enough to say, “Look, we think your site should be online. So we’re going to offer you some extra protection.” And so, they’re sitting—they’re in place and they take a lot of the flak for me. So—
I know there are other security bloggers out there. Of course, famously, Brian Krebs who’s an awesome security blogger. His site has been attacked many, many times because he’s unmasking the identities of cybercriminals and they don’t like that very much, do they?
Ran: Obviously not. But that is just interesting, that in your case, you had an organization that helped you, volunteered to help you. But that says—actually that—if you’re not as famous maybe as Graham Cluley, I mean a DDoS is a grave threat since it would really put your—crush your site. I mean it is a real threat to the ordinary man.
Graham: Yeah. It depends on—yeah. It’s true. I mean if you are—
Ran: If you are a small business and you can’t pay—
Graham: If you are a small business or if you’re an individual, then if someone tags you of a DDoS attack and they’re determined to keep you offline, that’s very difficult to handle. And so you will have to speak to your service providers to see what kind of assistance they can give you to try and prevent that from becoming a problem. One solution might be—it depends what you’re doing. If you’re just running a blog, for instance, you may decide, “You know what, I’m going to move my blog to WordPress.com and I’ll be part of that empire,” which is very well-protected in terms of DDoS attacks. Or things like Google’s blogger service, for instance, and then it’s like Google is protecting you. But some people like me like to run their own site and being in control of it. And so, we have to handle our own protection that way.
But, yeah, it would be very difficult if you’re a small business, if someone wanted to do that. And, of course, if you want to attack a website with a denial-of-service attack, it’s not hard to do. You don’t need to be technical. All you need to do is pay. You just need to find the right website and pay so many bitcoin and tell it where to attack and off it will go because these botnets are available for hire.
Ran: Speaking of paying for what is known today I think as a cybercrime as a service, what do we know now about the ecosystem—the crime ecosystem behind the scenes. How does the crime scene look like behind the scenes?
Graham: Well, it’s incredibly matured because it used to be just of lone hackers in their bedroom which, of course, the media would love to still present these things as, but now we have organized criminal gangs. And, yes, you might have some people who are nerdy with the neck beards or whatever who are into computers and they’re the ones maybe who are doing the coding. But you will have other people and other businesses who will provide them services to help support the cybercriminal activity. So they could be, for instance, providing hosting services for websites. They could be helping running the service or making sure that the service remain online.
There are some companies based around the world in jurisdictions where it would be very hard to get those service shut down and so they’re still allowed to continue to work. You will have people whose jobs it is to take the credit card details and create fake credit cards. You could have people who may be helping to actually act as money mules, moving money out of accounts, for instance, and they’ll go into cash machines and jackpot in those machines in order to take cash away.
So, you have really all levels—you know, this is big organized crime. These are like companies now, some of these guys working. The difference being is that they don’t all go to work in the same office. They may not even know each other because a lot of these groups will be virtual and they may be based in other countries and even if you wanted them to, they wouldn’t be able to tell you quite often the names of the other individuals who they are working with, but they’re all working to a common goal which is to steal your money or to steal your company’s secrets.
Ran: And one of the things that really influenced the rise of cybercrime in that sense is bitcoin, which is basically untrackable money. Do you think that there is any way to—I don’t know how to phrase it—to curb the threat of bitcoin in that sense? Or can we—can governments in any way influence that kind of cryptographic currency in a way that can, you know, mitigate that threat?
Graham: I don’t think there’s much chance of that. I think you can’t argue with maths and—what we’re fighting there—I mean there’s obviously all kinds of good things which can be done with bitcoins but let’s not dispute that, right? It’s not the actual currency itself which there’s any problems with, but—and the big benefits to be able to make anonymous purchases and transactions and so forth in some scenarios.
But, you can’t fight maths. 2 and 2 is always going to equal 4 and bitcoin is just based upon mathematics and cryptography. And provided that those algorithms are done correctly and provided the implementations are done properly and haven’t been tempered with and the software you’re using hasn’t been meddled with in some way, then I don’t really see what can be done about it.
Now, there have been problems sometimes with some of the bitcoin exchanges which people use and, of course, some of those are being hacked or some of those have had funds mysteriously withdrawn from them which perhaps they shouldn’t have done, and so that may be one way to control to some extent, but you’re just going to see other ones popping up elsewhere.
Ran: And, we were discussing earlier your incident with Gigabyte. And today’s malware authors and crime syndicates are much more mature as you said and dangerous. Do you think that if today you had that sort of attention from a cybercriminal that would take attention to you personally, will you be more afraid than you were from the silly encounters of the ‘90s and early 2000s?
Graham: Yes, I would.
Ran: Afraid for your own security in a sense.
Graham: I think it would be sensible to be more worried about it. I think the line of work I do is probably not putting me on the frontline of targets, I think, because it’s not like—I mentioned Brian Krebs earlier, right? Who I think a lot of us look up to and has put himself in danger. He’s gone to extraordinary lengths to find out details as to who is behind particular cybercrimes in the investigations he’s done, and the criminals have attacked him in response and done all kinds of unpleasant things to try and make his life more difficult. He’s someone who taught himself Russian in order to understand what the bad guys are talking about in cybercrime forums, and that’s not something I’m going to be doing anytime soon knowing my affinity with languages.
But, at the same time, I know that when I left my last company in order to work on my own, one of the first things I did was I went to the police and I said, “This is what I’m doing, and there’s the potential for me to be of interest to organized criminals” and they were able to help me, for instance, keep some of my personal information classified in terms of things like company records and so forth. One of the problems I have is my name is quite unusual. So, if you really want to find out where I live, you kind of can.
Ran: Why is it so unusual? I mean what, surname, Cluley?
Graham: Yeah.
Ran: Is that—
Graham: It’s very unusual surname, yeah.
Ran: I didn’t realize that.
Graham: Yeah, yeah, yeah, it is. It’s not—yeah. I think I’ve only ever met one other outside of my family in all my time. So, it’s pretty unusual and Graham is hardly the most normal name in England either. It’s not that common. So, that doesn’t help. And, of course—
Ran: Well, I’ve got—I’ve got the opposite problem.
Graham: Yeah, yeah.
Ran: Surname Levi, it’s so common. Nobody can find me.
Graham: Yes, yes. Exactly, yeah. Fantastic for you. Fantastic. Not so good if you’re trying to Google yourself, but—
Ran: Exactly.
Graham: But, yeah, I mean—you know, it’s something I think about and I have a young family and, you know, I want to be sensible. But, I think the kind of work I’m doing these days, I wouldn’t be of that much interest to the typical organized criminal. They wouldn’t want to draw attention to themselves I suspect by targeting someone like me. But, that is a crazy world out there these days.
Ran: And when you went to the police—yeah. When you went to the police as you told us, what was their initial reaction? Did they understand what you’re talking about?
Graham: They understood what I was talking about, yeah, because what I did was I took some examples of what had happened to other cybercrime bloggers and other commentators. So, I was able to provide them with evidence as to what had happened specifically to Brian Krebs where, for instance, they’ve had drugs delivered to his home. They’ve had armed SWAT team sent to his house, you know, all kinds of unpleasant things have happened to him which I wouldn’t want happening to me and my family.
I have had incidents in the past—there was a time—I don’t know if it was a virus writer who did this but someone took my photograph and they created a fake account on Facebook and they posted really unpleasant things on Facebook about child abuse and stuff like that. And as—
Ran: It could be a serious thing.
Graham: Yeah, it could.
Ran: It could hurt your public image.
Graham: At the time—well, at the time, I was actually on holiday in—where was I? I think I was in—not Thailand—Vietnam or something like that. Cambodia. I was in Cambodia. That’s right. And so I wasn’t on great internet connection anyway and I began to get these messages from my company that the CEO had been contacted by people saying, “Graham Cluley has been saying, you know, this, this and this on Facebook.” I mean introducing about them on my HR department who received emails. So people were so upset about someone who they believed to be me was posting on Facebook and recognized the picture and said, “That’s Graham Cluley. He works for so and so.” And so they would contact my company. My wife received messages saying, “We know where you live and we’re going to—” I received messages saying they’re going to shoot my wife in the head because they were so offended as to what this person was posting. And, Facebook—
Ran: This is very serious. I mean—
Graham: Yeah. It was horrible. It was absolutely horrible. And they said they were going to burn my house down and all sorts of things and I was in Cambodia at the time. I was far away from England. And—
Ran: How did you feel about that, being so far away?
Graham: I felt terrible. And so, what I did was I contacted Facebook and I said, “Someone has taken my photograph and they’re posting all these things and they’re saying that I’m pedophile and they’re riling people into, you know, getting—” My company was fine. They knew it wasn’t me but, you know, people were making unpleasant threats, and Facebook would do nothing. They said “If you’ve got a problem, you should go to the police, if people are making threats about you.” And I thought, “What kind of community is this that you’re not doing anything about this?” And the only point where I could get Facebook to care was not when I said they’re claiming that I’m a pedophile or they’re making death threats against my wife. The only point at which they cared was when I said, “They’re using a photograph of me which is the copyright of my company.” And then they said, “Oh, copyright infringement. We’ll do something.” And I was—
Ran: It’s so silly.
Graham: I was disgusted. Well, I was pleased that they did then, but I know other people this has happened to where fake Facebook profiles have been used with their photographs or maybe someone they may have offended but I remember one young woman, someone obviously had a vendetta against her and they posted messages claiming she was a prostitute and asking people to phone her up. And she just got so much harassment and so many unpleasant phone calls. And, you know, her reputation was being destroyed and I had reputation was being destroyed and I had the advantage that I was known in the computer industry. I could go to the press and kick up a stink and say, “Facebook aren’t doing anything and this is how Facebook have treated me.” But regular members of the public have a much harder time and I’ve had a bad taste in my mouth about Facebook ever since.
Ran: This is a very interesting story. I mean I used—in my imagination when I mentioned a threat from cybercriminals, I was threating about what most people would probably think about a violent threat. Now you’re describing a sort of threat which is non-violent in that sense but can get violent in unconventional ways.
Graham: Yes. Well, I don’t know that this particular attack was inspired by computer criminals or, you know, it could have been someone else, who knows, maybe someone just didn’t like me for some reason.
Ran: Krebs experience shows that cybercriminals can and do use these tactics.
Graham: Yes.
Ran: So it’s very interesting.
Graham: It’s potential possible. I don’t know who is responsible for it. But just as company’s reputation can be very badly damaged by hackers who might be stealing information or exposing something or even spreading a lie about a company or defacing a website. I’ve seen—I remember, for instance, years ago, Symantec’s website got defaced and they posted a message up on the Symantec homepage claiming that the website was infected by a virus, which obviously would be very, very bad news for Symantec, right? You know, “Come on, those guys can’t even get that sorted.” Now, it turns out it wasn’t infected by a virus. It was just a defacement of a website. It was embarrassing graffiti but basically harmless. But the damage it’s done to their reputation and they probably have some users who went there, saw that and thought, “We’re not going to use that product anymore” or “We need to go and buy something else because they can’t be trusted.” And so, yeah, I mean—
Ran: There was damage, yeah.
Graham: There is usually damage from these things even the viruses from way back then, the green caterpillars. There’s still damage being done and there’s downtime and—as people are panicking and trying to recover from an incident, computer systems come down, work grinds to a halt, you can’t do your regular business because you rely on the computer network. It’s like these hospitals who keep on getting hit by ransomware and hospitals are often very poorly financed in terms of IT and they haven’t had the investment there. And then, you know, they may get hit by something and their systems come down for a while and they’re having to use pen and paper. Well, there’s a real impact on the patients and the care and the number of operations which can be handled, and these are organizations which are already enormously stretched and their lives have just been made more difficult because of criminal hackers.
Ran: Yeah. This is very interesting, extremely interesting. So one last question, looking back at all your rich career in handling all sorts of cyber threats, which of the malware or threats or whatever that you remember is most striking, maybe most sophisticated, most amusing, most interesting in any sense?
Graham: Oh, wow. I think the one which—the biggest and most memorable for me is the love bug, the ILOVEYOU worm, which was written in the Philippines by a guy called Onel de Guzman and released on May 4, 2000. And it was a simple visual basic script virus which would forward itself to the people in your address book. But what was clever about it was the social engineering and that’s what got people all around the world to open it. And the social engineering was the subject line which was “I love you” and in the body of the email, it said, “Kindly read the attached love letter coming from me.” And if you received that email from that cute girl in the accounts department, you were going to click on it because you think, “This sounds good.” Or if you received it from your boss who wasn’t at all sexy, you were going to open it and you’d think this is either him joking, you’d think, or you’d think this is going to be so juicy. He’s got a crush on me, or whatever it is. You were going to open it, and the words are—
Ran: It’s irresistible.
Graham: It’s irresistible. And the words “I love you” are understood around the world. It’s not—you don’t even have to be an English speaker. You know the words “I love you” whatever language you speak. You hear it all the time in the movies. I love you. That was the genius of it, and it spread around the world like wildfire. And unfortunately, they didn’t have sufficient computer crime laws in the Philippines and the guy got away with it and he’s never been punished. But—
Ran: What kind of damage did the love bug do?
Graham: Well, it just generated an enormous amount of email and it spread and it clogged up email systems and just, you know—it’s huge amounts of email being spread around. It wasn’t designed to do any damage in terms of damage to your computer, but what many forget was it was actually designed to steal a piece of information for you because Onel de Guzman had developed this piece of malware with the intention of doing it as a project for his college, and he proposed to his college—in the thesis, he said, “Look, what I want to do is I want to write a program which gives people cheaper internet access.” And originally the college was very keen on this until he explained he was going to do it by writing a virus which stole people’s internet usernames and passwords, which—yes, would get you cheaper internet access but may not be completely ethical.
So the college didn’t let him write it but then he wrote it on his own and he released it. So, millions and millions of computers around the world are infected by this virus and it is going into their settings and it’s stealing that internet access, their dial-up usernames and passwords because we were all on dial-up then. We weren’t really on broadband. And it was sending them to de Guzman in Manila in the Philippines. Now this is the year 2000 in the Philippines. Can you imagine what internet connection was like? Pretty—
Ran: Poor.
Graham: –poor. And he’s now got tens of millions of computers around the world all trying to send him their usernames and passwords. So he had effectively denial-of-serviced himself. And I miss those days.
Ran: Own goal, that’s the definition of an own goal.
Graham: Exactly, own goal. Although, do you know, they actually made a movie. There is a movie of the love bug, a rom-com or something. I’ve never seen it unfortunately. I think it’s called I love you or P.S. I love you or something like that. But, they did get an American style—so there is a movie out there all about a couple who fall in love because they received the ILOVEYOU virus and there’s a misunderstanding or something like that. So some good came out of it.
Ran: Graham, that was an amazing talk. Thank you very much.
Graham: My pleasure talking to you too.
 Latest episodes
Latest episodes 

 Subscribe
Subscribe 









