Season 1 / Episode 4
2016 is known throughout the circles of information security as “The Year of the DDoS attacks”, and rightfully so: 5 large scale DDoS attacks - ‘Distributed Denial Of Service’ - shocked the technology world. In this episode of Malicious Life, we examine how the power of the internet itself can be harvested and deployed to take down major companies and websites.
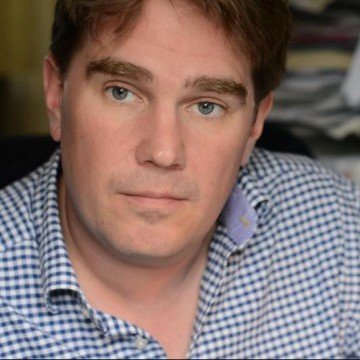
Hosted By:

Ran Levi
Born in Israel in 1975, Ran studied Electrical Engineering at the Technion Institute of Technology, and worked as an electronics engineer and programmer for several High Tech companies in Israel.
In 2007, created the popular Israeli podcast, Making History, with over 9 million downloads as of July 2017.
The author of 3 books (all in Hebrew): Perpetuum Mobile: About the history of Perpetual Motion Machines; The Little University of Science: A book about all of Science (well, the important bits, anyway) in bite-sized chunks; Battle of Minds: About the history of computer malware.
Special Guests:

Yossi Na'ar
Yossi Na’ar, Chief Visionary Officer and Co-Founder at Cybereason, is an accomplished software developer and architect. During his 20 years of industry experience, Yossi has designed and built many products, from cutting-edge security platforms for the defense industry to big data platforms for the AdTech / digital marketing industry as well as the Cyberason in-memory graph engine.
Graham Cluley
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s, having been employed by companies such as Sophos, McAfee and Dr Solomon’s. He has given talks about computer security for some of the world’s largest companies, worked with law enforcement agencies on investigations into hacking groups, and regularly appears on TV and radio explaining computer security threats.
Episode transcript:
Hello and welcome to Malicious Life. I’m Ran Levi.
2016 is known throughout the circles of information security as “the year of the DDoS attacks”, and rightfully so: 5 large scale DDoS attacks – ‘Distributed Denial Of Service’ – shocked the technology world. The biggest was the attack on the American DNS provider Dyn, which affected some major websites such as Twitter, Etsy, Github and others- and made the danger of DDoS attacks known to the public and to decision makers.
An Old Cyber Threat
Information security experts weren’t surprised, of course: they’d been dealing with DDoS attacks for years. They are one of the oldest cyber threats- but also one of the most complex and difficult to deal with. Why? This will be the question we answer in this episode. We will discuss the evolution of DDoS attacks from a tool used to express political ideas and ideological resistance – into a weapon used by cyber criminals. We will try to understand why this threat is such a hard nut to crack; and eventually, we will discuss the possible solutions, especially some radical and highly controversial ones – like purposely destroying consumer devices.
The basic idea behind a Denial of Service attack is so simple that you’ve probably seen it in action many times. An ice-cream truck rolls down the street, its speakers blasting loud music, and instantly a bunch of sweet toddlers playing in the playground become a pack of wild animals. I’ve seen this happen, it’s not a pretty sight. The children charge at the vendor, bombarding him with requests for ice cream bars and popsicles. But since there is only one vendor and many children, he cannot serve everybody at once, and therefore, some of the children will have to wait or will never get their ice cream. In other words, they’ll experience a denial of service. This simplicity translates well into the virtual world: just like the ice cream vendor, a web server can only serve a limited number of users before reaching the end of its bandwidth, and other users will only receive an error message.
The Electronic Disturbance Theater
In the second half of the 1990s, a group of social human rights activists called the Electronic Disturbance Theater or EDT was operating in Europe and the US. The members of the EDT were inspired by the Civil Rights Movement’s actions in the 1960s, which acted to promote desegregation by organizing nonviolent protests called Sit-Ins. Young people of all races would arrive at restaurants and places of business that refused to serve black people, sit down, and simply refuse to leave. Getting beat up, arrested, or threatened did not deter them. The quiet and non-violent Sit-In protests proved themselves very effective and changed public opinion in favor of their struggle: many businesses gave in and started serving black customers.
Members of the EDT decided to transfer the Sit-In into the virtual world. Yossi Naar, co-founder and Chief Visionary Officer at Cybereason, explains what attracted the social activists towards the idea of Denial of Service attacks:
“Denial of service attacks […] always existed. It’s like, in a sense, the cheapest thing that you can do. The basic form of a denial of service attack is like if I have a computer connected to another computer and I just bombard it with traffic or bombard it with whatever and cause it to fail, cause it to stop, cause it to be unable to provide a service that’s intended to provide.
There are more sophisticated denial of service attacks whereby you would exploits a vulnerability in a service that would cause it to overload in some way or shutdown or restart. These are closer to what we would call hacking cause denial of service attacks is like really the lowest form of attacking someone.“
The trigger for the EDT’s virtual attack was a violent event in Mexico where dozens of citizens were murdered as part of the Mexican government’s fight against a revolutionary organization called The Zapatista Army of National Liberation. Members of the EDT wanted to draw public attention to the Zapatistas’ cause by performing a Denial of Service attack that would crash websites run by the US and Mexican governments. After all, what is a Denial of Service attack if not a kind of virtual Sit-In, in which a protestor enters a website and refuses to leave…
FloodNet
The problem was that one computer can’t create enough information traffic to overload an internet server. It takes more than one child to overwhelm the ice cream vendor, so to speak. Members of the EDT had to draft for their cause a few thousand computers that would simultaneously “bombard” the targeted website. This kind of coordinated attack by a number of computers is called a Distributed Denial of Service attack, or DDoS.
The tool used by the EDT was a simple Java program called FloodNet, which ran on the user’s browser. The only thing the program did was refresh a URL address every few seconds- not much different than manually hitting the browser’s Refresh button over and over. In 1997, close to 10,000 EDT supporters turned on the program simultaneously and directed it towards websites such as the White House homepage, that of the Mexican president, the Mexican stock exchange, and others. The flooding tool did its work, and some of the websites indeed crashed for a few days. By the way, when the EDT tried the same trick on the Pentagon’s website, they discovered that the clever people on the other side had a surprise of their own waiting for them: a counter attack that made their browsers display multiple error messages – and crash.
The Desire to Disrupt The Status Quo
And still, the EDT’s virtual protest was effective and raised public awareness to the Zapatistas’ organization. Ten years later, the hacktivist group Anonymous used the same idea in order to crash the websites of the Church of Scientology, and they too had great success. Here’s Yosi Na’ar:
“DDoS is a bit more sophisticated because it requires a lot of resources or sometimes requires a lot of resources. For the Anonymous attacks for example, there’s a tool called LOIC – Low Orbit Ion Cannon, that they call it. It’s basically this thing that you can run on your computer and they ask like a lot of people to run on their computers and their computers that they control, and sort of hand over a coordinate control to a centralized system which would then form a DDoS attack. This is usually aimed at some website to topple it.
Now, in very broad strokes, this sort of taps into the part of hacker culture which is a little bit anarchistic, that always sort of exists in the background. And for the anarchist, there’s the desire to disrupt the status quo and to protest against the existing situation.”
The DDoS proved itself, it would seem, as an effective tool for Civil Disobedience campaigns. But as Yossi mentions, this idea also had a significant disadvantage, which was that in order to organize a successful DDoS attack, thousands or even tens of thousands of users need to be convinced to install software such as Low Orbit Ion Cannon on their computers, and activate them more or less at the same time, which is no easy feat.
But there’s also the option of recruiting computers for DDoS attacks without the will, or even knowledge, of their owners. The first programs that allowed an attacker to seize control of a computer and to use it for a DDoS attack appeared in 1997.
MafiaBoy
Canadian Michael Calce was only 15 when he discovered one such program, called Trinoo. Calce, whose online nickname was MafiaBoy, was part of a group of young hackers who called themselves TNT, and waged online battles against other groups of hackers: who can break into more networks, who can crash more computers, etc. Calce’s weapon of choice was Denial of Service: he would break into computer networks like those of universities and similar organizations, and use them to execute DoS attacks on the computer networks of rival groups. In his autobiography, Michael Calce later wrote of the role that Denial Of Servcie attacks filled in the Hacker Wars:
“We were trying to see whose missile could go further faster and carry a more damaging payload. Instead of warheads, we were using packets. It was a matter of who had the most bandwidth, the most servers, and the best software to use in attacks.”
Trinoo was a powerful weapon in Calce’s hands. It was like going from using a pistol to a Howitzer cannon.
“Trinoo had ushered in an era of distributed denial-of-service (DDoS) attacks, the ability to launch a coordinated attack from a variety of networks. I was now thinking along the lines of a mass distributed denial-of-service (MDDoS) attack. In basic terms, my goal was to chain my large network of servers together so that I could easily launch one massive attack. Rather than having to launch a separate attack from each server, I wanted to be able to centralize and make them work as one. This would heighten the impact and also save me a lot of time. The idea was to have one so-called master, and multiple slaves, or “zombies” – the term used to describe compromised computers and servers that have been linked together in a vast network, or botnet.
Because of my previous tests with Trinoo, I knew that small corporate or university networks would instantly crumble in the face of my new, more forceful attack. That wasn’t what I wanted. I needed to go up against a major network to see how powerful [I was]. I was convinced the only way to test my new tools and networks was to aim big. Otherwise, I wouldn’t get the results I needed. After some research, I saw that a search engine would be my best target because it deals with a huge amount of internet traffic. At the time, Yahoo! was the world’s top search engine.”
In other words, Calce was planning to wage a DDoS attack against the internet’s largest search engine as a “weapons test” before attacking other 15 year olds. If it sounds childish, it is- MafiaBoy was a teenager, and teens as any average parent would tell you- are basically human-sized bags of hormones, adrenaline, self-importance, and under-developed brains. As Calce, who had no idea what he is getting himself into, says:
“In retrospect, I see that I had no clue as to the potential impact of what I was doing. At the time, Yahoo! had one of the biggest websites and networks on the web. It was also a multi-billion dollar company that was seen as a bellwether of the technology industry. I should have seen that any kind of attack against Yahoo! would have been big news, even if it failed. But those factors didn’t register in my mind. I had built something remarkably powerful and wanted to put it to the test. I was a kid with a new toy.”
“It Almost Seemed Too Easy”
For his planned attack, Calce recruited approximately 200 computers from 3 different university networks he broke into. On February 7th, 2000, he ordered all the computers under his control to attack Yahoo!’s homepage and left for school.
Yahoo!’s homepage crashed, and millions of web surfers received error messages. News broadcasts around the world reported this dramatic attack against the most important website on the internet: More than a gigabit of information per second. But Calce, who was sitting in class, had no clue that this was happening.
“Arriving home just before 4 P.M., I discovered that Yahoo! had been knocked offline. […] I sat in front of my monitor, frozen in a state of shock. This was not at all what I had expected. I combed through my reports to see what had happened. It almost seemed too easy.”
Drunk with his incredible new-found power, Calce forgot that the attack on Yahoo! was just a weapons test, and launched other DDoS attacks against CNN, eBay, and Amazon.
“I had kept the attack on CNN going for close to two hours, but Amazon.com fell so hard, so fast, that I took mercy on it. It was like a hamster on a wheel was running its network. I kept the site down for about an hour, then called it off. I felt like a Rottweiler mauling a Maltese.”
In forums and IRC channels, feverous discussions were taking place. Everyone was talking about the “legendary” hacker who managed to crash the two largest websites within two days. Calce was elated. He felt like an internet god. But what the power-crazed Calce didn’t know was that the FBI had an undercover operative inside the IRC channels who was following the teenager’s boasts. The FBI put the hints together and uncovered MafiaBoy’s true identity.
After Amazon, Calce went after Dell’s homepage – and it was this attack that sealed his fate. Unlike Amazon and Yahoo!, Dell didn’t publish that they were attacked, and when Calce bragged about it in the underground forums, it served as clear proof of his guilt, since there was no way of hearing about it from the media. The police raided Calce’s house and arrested him. He was trialed and convicted on 58 counts of online crime- but due to his young age, he was only sentenced to 8 months in prison and a tiny fine. Growing up, Calce changed his ways and is now working as an information security advisor.
Infected Computers To Valuable Resources
Calce’s case was a wake-up call for the law and order authorities in the US and the rest of the world. For the first time, everyone could understand the true nature of DDoS threats: if a 15 year old boy with 200 computers could threaten the biggest websites in the world- the internet has a real problem.
And it just got worse. In the early 2000s, a new type of malware appeared on the stage: Net Worm, or Worm in short. A worm, unlike the “classic” viruses we’ve gotten to know over the last few episodes, doesn’t need the help of humans with disks in order to spread: the worms leap from one computer to the next by way of the networks connecting them, without human mediation. Because of this, worms were able to spread throughout the internet much faster than the viruses. If a typical 90s virus needed a few months to infect computers all over the world, the Slammer worm, in 2003, did it in only 10 minutes. It’s no wonder that within a few years, worms became the distribution method of choice for cyber criminals, pushing out the viruses in the process. Worms such as Bagle, NetSky, MyDoom and Sasser crashed on the shores of the internet like a tsunami and infected millions of computers.
Many of these worms contained Payloads, which added the infected computers to BotNets, under the control of one single BotMaster. The operative word here is ‘control’: the fact that the BotMaster had the ability to control the infected computers completely transformed the underground world of virus writers. It turned the infected computers into a valuable resource – one which existed only in the virtual world, but isn’t much different than natural resources such as oil or gold. And like in the real world, an entire ecosystem developed around this resource as well.
In the previous episode, we touched upon one aspect of this new economic environment: spam, and how criminal elements used Bot networks in order to make millions of dollars from junk mail. Another aspect of this new economy was the DDoS: Bot operators learned that money could also be made through DDoS attacks. It didn’t take long for services to pop up, offering BotNet rentals by the hour for anyone wanting to launch a DDoS attack. Graham Cluley, the information security expert we’ve met in previous episodes, discusses the influence this development had on cyber-crime:
“Well, I think if I recall correctly, the DDoS attacks really began to become influential round about the time of the rise of the botnet. So, when the hackers realized that they shouldn’t just compromise computers to steal passwords, but they could actually compromise them to hijack resources, to send spam and to have all of those controlled at once. And then you think, “Well, we don’t just have to send spam from these computers,” which is one way of monetizing them. “We can also extort money by launching DDoS attacks as well.”
And, you know, there is so much being done and so many attacks which are constantly happening against websites now. There’s a thriving industry of companies who are trying to mitigate DDoS attacks as well. And there are companies who are prepared to pay a large amount of money to stop a DDoS attack, I’m afraid.
So—I can kind of understand that in a way because they want to do business. If a gambling site is targeted with a DDoS attack just before a big sporting event, and they think, “If we aren’t running on this particular day, we are going to make—we’re going to lose a lot of money.” They’re making a pragmatic business decision to pay the extortionists. I don’t like it, but I can kind of understand it.”
The best demonstration of the power of BotNets for hire was provided in 2007, because of ….a statue.
The Bronze Night
Estonia had been under Soviet occupation for many years, and as the USSR fell apart, the new nation started on a new road. Within a few years, Estonia developed a prosperous hi-tech industry, and the internet became an integral part of the lives of many citizens, who were paying their taxes and getting their news online.
But the days of Soviet rule left many open wounds in Estonian society. About a quarter of the Estonian citizens were Russian, connected to Russia by strong cultural ties, and their presence was unwelcome in the eyes of Estonian nationalist extremists, who viewed them as a relic of the cruel Soviet occupation. These tensions created strong frictions within Estonian society, which culminated in April 2007, due to the government’s decision to move a bronze statue, which until then was placed in the center of the capital city Tallinn to a cemetery on the outskirts of the city.
You may ask yourself: why would the Estonian government make such a big deal about one statue? Well, the statute in question was not some random work of art, but a monument for the fallen soviet soldiers who died in Estonia during World War II. The Russians view World War II as one of the landmark events in their national history, and therefore, the decision to move the statue to a remote location was seen as a great insult. A series of violent demonstrations broke out in the streets of Tallinn, carried out by Russian-Estonians. The demonstrations were nicknamed “the Bronze Night”. An uproar arose in Russia, too, accusing the Estonians of being rude and ungrateful for the sacrifice made by the heroes of the great war. In many Russian websites and forums, insults were thrown at the Estonians and many web surfers were calling for revenge.
And revenge soon followed: dozens of large Estonian websites, from major newspapers to government websites, parliament and banks- all fell victim to massive DDoS attacks, causing all of them to crash almost simultaneously. The attacks continued for about 3 weeks and reached their peak on May 9th, the official Russian holiday of Victory Day, commemorating Russia’s victory over Nazi Germany. Russian patriotism was translated into DDoS attacks by approximately one million computers simultaneously, which crashed many government and private websites.
Although Estonian politicians accused Russia of being directly responsible for these attacks, most security experts who examined these attacks estimated that they were private endeavors: individuals who hired BotNets for limited times- a kind of digital version of the riots on the streets of Tallinn on Bronze Night.
This cyber-attack on Estonia made it clear once more, just how serious the threat of DDoS is, and how easily criminal or anarchist elements can disrupt the digital lives of many civilians. Furthermore, the attack on Estonia demonstrated that not only commercial websites such as online stores or search engines are vulnerable to DDoS attacks, but also essential government infrastructure and services such as banking services, media, and others. This weakness provides immense power in the hands of smaller and militaristically weaker countries.
The DDoS That Almost Broke The Internet
This last point received additional emphasis in 2013, following an unprecedented DDoS attack against Spamhaus, a non-profit organization that helps other organizations and companies to filter spam. This attack was nicknamed The DDoS That Almost Broke The Internet.
Naturally, spammers aren’t exactly fond of Spamhaus, and its servers suffer DDoS attacks and break-in attempts on an almost daily basis. But the DDoS attack that began in March 2013 was much larger than the ones the engineers at Spamhaus were used to dealing with: 10 gigabits of information streamed into Spamhaus’ servers every second – 10 times the bandwidth that Michael Calce was using in 2000 that was able to crash the biggest websites on the internet. Spamhaus was unable to deal with such a monstrous attack and called upon CloudFlare, a content delivery network (CDN) that also provide anti-DDoS defense services.
CloudFlare, which has servers in dozens of countries around the world, handled the attack easily, and Spamhaus’ website went back online. But the attackers didn’t give up, and pressed the pedal to the metal in order to knock down CloudFlare’s network as well. The information volume of the attack jumped to 100 gigabits per second, and then to 120. It was one of the largest DDoS attacks that CloudFlare had ever known. But the company endured.
The attackers realized that a frontal assault wouldn’t succeed and changed their tactics. At this point, we should remember that the internet is a net made up of many smaller networks interconnected in different points- just like intersections connecting roads. Some of these points are major intersections connecting important networks. These connections are called Tier 1 Networks, and we can think of them as critical intersections connecting busy inter-city highways. Spamhaus’ attackers directed their DDoS cannons towards some of those Tier 1 networks, flooding them with 300 gigabits per second: the largest DDoS attack ever recorded. It is important to understand the ramifications if those Tier 1 networks had crashed: hundreds of millions of people would have encountered serious difficulties in surfing many websites, some not even related to Spamhaus and CloudFlare. Luckily, these networks were able to withstand the attack. Barely.
And then came 2016, ‘the year of the DDoS attacks’. Large-scale DDoS attacks of over 100 gigabits per second leaped 138% compared to the previous year. One of those attacks was on the website of journalist Brian Kerbs, and it almost took down Akamai- a content delivery network service provider that prides itself on the fact that approximately a third of internet traffic goes through its servers daily. Kerbs was saved only when the great Google agreed to take his website under its wing. And then, on October 21st– the biggest attack of all, ‘the mother of DDoS attacks’, was launched on Dyn, a DNS service provider, with 1.2 terabits of information per second- 1000 times more than the bandwidth MafiaBoy was using at the time, and twice what was used against Kerbs. Big websites such as Reddit, Twitter, CNN and others went down for hours.
IoT BotNets
This leap in the power of DDoS attacks was made possible due to a new resource that was added to the arsenal of cyber criminals: Internet of Things (IoT) devices. These household devices such as security cameras, DVRs, smart TVs and similar appliances are characterized by two main qualities: they are smart- meaning that their cores hold computers with solid processing power and an internet connection, but they are also very cheap. So cheap in fact, that the manufacturers of such devices have no incentive to invest in their development more than the bare essentials, and in situations like these, security is usually the first thing that goes out the window. There are millions such devices online all over the world, and worms that spread quickly – such as the now infamous Mirai worm – take over such devices and recruit them to massive scale BotNets. Yossi Naar, Cyberreason’s Chief Visionary Officer, explains:
“The botnet was formed out of IoT connected devices, cameras, routers, whatever that have very crappy security. Basically non-existent security; usually you can just access them remotely, there’s no firewalls standing between you and the device which sometimes is the case because people don’t really know how to secure their systems. You can just log into it with whatever default password the device uses and if not, then there’s some minor hack that you can employ to gain control over these devices. Now, interesting – you would think that there are other things that you could do with all these cameras that you control, but what they have become are just a mechanism to, you know, as a sort of a paid server you can buy, these botnets rent them and aim them at this particular target for however long.”
Household consumers, the owners of IoT devices, aren’t even aware of the fact that their security camera or TV are taking part in a DDoS attack, since the devices continue to function, for the most part, uninterrupted. Furthermore, unlike home computers that are turned on and off throughout the day, IoT devices are usually turned on 24/7 and are available to the criminals’ needs, thus making IoT based BotNets even more powerful.
Game Changers
The attacks on Kerbs and Dyn proved that IoT BotNet are game changers. If anyone had doubts about the severity of the DDoS problem and the threat it poses on our digital lives- those doubts are now gone. Bruce Schneier, a well-renowned information security expert, said the following in his testimony in front of the Congressional Committee on Energy and Commerce:
“In many ways, the Dyn attack was benign. Some websites went offline for a while. No one was killed. No property was destroyed. But computers have permeated our lives. The Internet now affects the world in a direct physical manner. The Internet of Things is bringing computerization and connectivity to many tens of millions of devices worldwide. We are connecting cars, drones, medical devices, and home thermostats. What was once benign is now dangerous.”
As we’ve seen, DDoS attacks have been an issue for more than 20 years now, and threaten a wide array of vital services- from banking to healthcare services- but no suitable solution has yet been found. Some security experts, such as James Scott & Drew Spaniel from the ICIT Institute, believe that the solution is strengthening the defenses against DDoS attacks. In a report published by the two following the attack on Dyn, they state:
“As with all varieties of cybersecurity and cyber-hygiene, the key to an organization’s survival in an increasingly hostile threat landscape is preparedness and forethought. At the moment, organizations have few technical options to mitigate DDoS aside from anti-DDoS service, endpoint security, and filtering rules. Instead, organizations can improve their security posture by developing an actionable and practiced incident response plan or standard operating procedure for their personnel to follow in the event of an attack. These plans ensure a chain of communication and command, and they preclude rash short-term actions that could harm the organization in the long-term.”
Bruce Schneier, on his part, supports aggressive government regulation. In an essay he posted on his blog, Schneier says:
“The technical reason these devices are insecure is complicated, but there is a market failure at work. The Internet of Things is bringing computerization and connectivity to many tens of millions of devices worldwide. […] Many of these devices are low-cost, designed and built offshore, then rebranded and resold. The teams building these devices don’t have the security expertise we’ve come to expect from the major computer and smartphone manufacturers, simply because the market won’t stand for the additional costs that would require. […]
An additional market failure illustrated by the Dyn attack is that neither the seller nor the buyer of those devices cares about fixing the vulnerability. The owners of those devices don’t care. They wanted a webcam —- or thermostat, or refrigerator -— with nice features at a good price.
The sellers of those devices don’t care: They’ve already moved on to selling newer and better models. There is no market solution because the insecurity primarily affects other people. It’s a form of invisible pollution. And, like pollution, the only solution is to regulate. The government could impose minimum security standards on IoT manufacturers, forcing them to make their devices secure even though their customers don’t care. They could impose liabilities on manufacturers, allowing companies like Dyn to sue them if their devices are used in DDoS attacks. The details would need to be carefully scoped, but either of these options would raise the cost of insecurity and give companies incentives to spend money making their devices secure”
There is much wisdom in both these solutions, but there are also drawbacks. Readiness and correct education against DDoS attacks are a great idea, no doubt, however- what will small website owners do: those who haven’t the technological knowhow or means to defend themselves against such attacks? Good regulation is also a well-proven solution, but provided that most IoT manufacturers don’t reside in the US and infected IoT devices could be anywhere in the world, effective regulation will be quite a challenge.
A Tempting Solution
Another possible solution is an idea that has been circling the fringes of the information security world, from the very beginning of this industry. It is an idea that was repeatedly rejected because it’s considered extreme and dangerous- but it’s also so powerful and tempting, that it never entirely vanished. This idea is called A Good Worm.
The principle is simple: the bad guys are winning because they can reach any susceptible IoT device and take control of it without asking questions or permission. The good guys, on the other hand, can’t just knock on the door of anyone owning an infected device and ask them to fix it. A Good Worm is a malware that spreads throughout the internet in the same manner that the malicious ones do – but as soon as it takes control of a device, it fixes it. Instead of adding it to a BotNet, the good worm removes malicious code that might exist on the device, updates the operating system and fixes the existing security vulnerabilities.
I bet you’re starting to understand the power of this idea. Basically, millions of infected IoT devices can be “cured” within hours and the rug will be pulled from under the bad guys’ feet. It’s also not that complicated to execute. A talented developer could most likely do most of the work alone.
But the idea of the good worm was never accepted in the information security world, and most likely never will be. The reason is the same reason that a doctor walking down the street can’t just abduct any overweight person he sees, lock him up in his house and force him to eat healthy and exercise. Human beings have basic rights over their lives and possessions, and no one has the right- except in extreme cases- to violate those rights, even if it’s clear that this violation will benefit them in the long run. The hands of law enforcers are tied.
The Hero We Deserve
But, what about those who aren’t law enforcers? Batman, as you know, doesn’t consult the police commissioner in Gotham before he puts on the black mask and goes out to kick some butts… In recent years, some have decided to follow Batman’s legacy and take the law into their own hands. A group of anonymous developers calling themselves The White Team has developed a malware called Wifatch, which takes over infected IoT devices, removes the malware infecting them, and closes the communication channel through which such malware could penetrate the device in the future. In 2016, the team released Wifatch’s original code to the internet so other willing developers could assist. In the README file attached to the code, the writers added a chain of Q&A where they wrote the following:
“Q: Do you feel bad about abusing resources by others?
A: Yes, although the amount of saved bandwidth by taking down other scanning malware, the amount energy saved by killing illegal bitcoin miners, the number of reboots and service interruptions prevented by not overheating these devices, the number of credentials and money not stolen should all outweigh this.”
Wifatch doesn’t harm the devices it controls- not intentionally, anyway. I’m sure there are some in the information security community who are quietly cheering them on. But what is considered an act of good by one person, doesn’t necessarily match the morals of another, and in an absence of law- everything is allowed. In march 2017, another ‘good malware’ appeared. The name given to it was BrickerBot – and if you know what ‘bricking’ means, I think you already know where this is leading.
The John Doe who developed BrickerBot calls himself The Janitor- a nickname that discloses his motives. In an anonymous interview he gaveto bleepingcomputer.com, he said:
“Like so many others I was dismayed by the indiscriminate DDoS attacks by IoT botnets in 2016. I thought for sure that the large attacks would force the industry to finally get its act together, but after a few months of record-breaking attacks it became obvious that in spite of all the sincere efforts the problem couldn’t be solved quickly enough by conventional means.
I hope the unconventional actions by ‘BrickerBot’ have helped in buying another year of time for governments, vendors and the industry in general to get the current IoT security nightmare under control.”
The unconventional actions the Janitor is referring to are an attempt to fix the infected device and seal the security breaches, but if that doesn’t work, BrickerBot will destroy all the files on the device’s memory and thus disable it, or “brick it”, completely. Even a factory reset won’t help: it’s time to buy a new device. Janitor claims that he has destroyed 2 million devices in this manner, and many more will follow.
Janitor knows that he is harming the owners of the devices, and has no illusions about the repercussions of his actions. Remember the analogy I used before about the doctor abducting unhealthy patients? It wasn’t a random choice.
“I consider my project a form of “Internet Chemotherapy”. I sometimes jokingly think of myself as The Doctor. Chemotherapy is a harsh treatment that nobody in their right mind would administer to a healthy patient, but the Internet was becoming seriously ill in 2016 and the moderate remedies were ineffective. The side effects of the treatment were harmful but the alternative (DDoS botnet sizes numbering in the millions) would have been worse. I can only hope that when the IoT relapse comes we’ll have better ways to deal with it. […] The IoT problem is much worse than most people think.”
In this episode, we’ve followed the evolution of DDoS attacks- a problem that accompanied the internet since its very beginning. We’ve seen how DDoS attacks went from being a semi-legitimate tool for social protest to being a problematic toy in the hands of bored teenagers and then to powerful weapons in the arsenal of cyber criminals. Computers became a resource, and around this resource, a vast and intertwined economy was built. The adding of droves of IoT devices to the playing field has turned DDoS attacks into an even more tangible threat, and has encouraged vigilantes such as The White Team to take the law into their own hands. Some of these vigilantes have decided that the ends justify the means and that destroying the property of innocent civilians is a legitimate course of action in order to protect the safety of the internet.
You know what? When I review the history of DDoS and the continuing failure to deal with it throughout the years, I ask myself if it’s possible that the Janitor might not be the hero that we need – he just might be the hero we deserve.
 Latest episodes
Latest episodes 

 Subscribe
Subscribe 













